
WhatsApp Spyware Detection — Find and Remove Surveillance
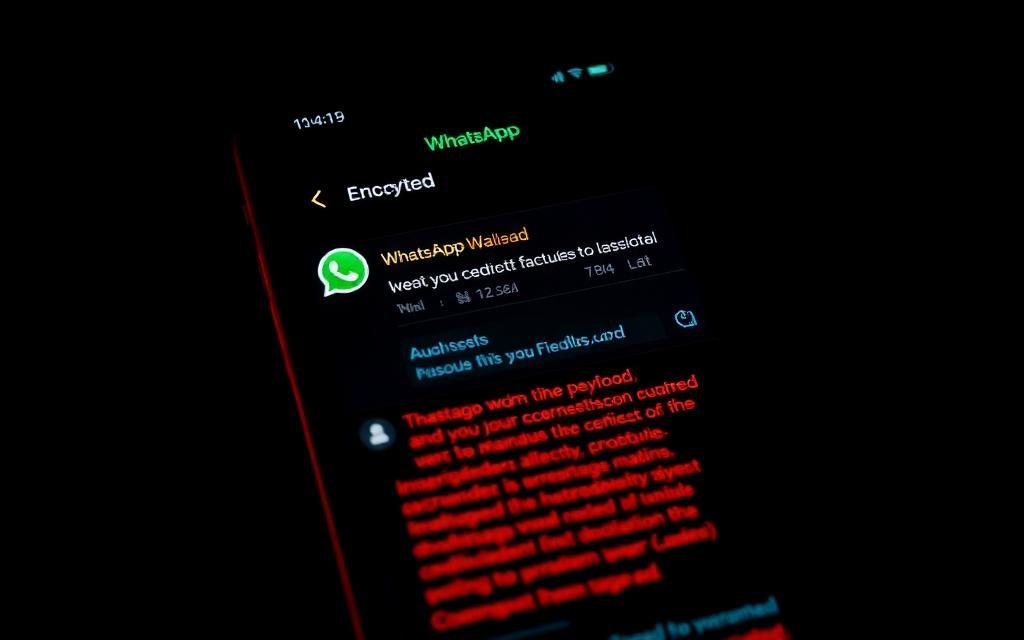
WhatsApp's end-to-end encryption protects messages in transit. It does nothing to protect the device that decrypts them. We find the surveillance layer attackers actually use, on the device and in the linked-device list.
How WhatsApp Actually Gets Spied On
WhatsApp's Signal-derived end-to-end encryption is not the weak link. In every real-world case we have investigated since 2022, the compromise occurred at one of four points outside the cryptography itself, and understanding which one matters because the response is different for each.
Vector 1 — Linked Devices abuse. WhatsApp Web and the new multi-device architecture allow up to four secondary devices to receive a real-time copy of every message. An attacker with sixty seconds of physical access can scan the linking QR code from their own laptop and walk away with a permanent feed. The sessions persist for months unless explicitly revoked.
Vector 2 — Mirror apps and modded clients. WhatsApp Plus, GBWhatsApp, FMWhatsApp and similar mods often ship with surveillance backdoors that exfiltrate the local msgstore.db to a third-party server. They look identical to real WhatsApp, often with extra features, which is why they are popular and dangerous.
Vector 3 — Device-level spyware. Pegasus, Predator and consumer stalkerware do not break WhatsApp's encryption — they screenshot the decrypted screen, harvest the SQLite database directly from the file system, or hook the rendering library via Frida-style instrumentation. From the user's perspective the result is identical to a 'WhatsApp hack' even though WhatsApp is not the vulnerability.
Vector 4 — Account hijack via SIM-swap. The attacker ports your phone number to their SIM, registers WhatsApp with the SMS code, and inherits your contact list and group memberships. They cannot read history (it lives encrypted on your old device) but they can impersonate you to everyone you know — often the more damaging outcome.
- Unknown entries in WhatsApp → Settings → Linked Devices
- Battery drain spike with WhatsApp in 'Other' category of usage stats
- Status messages or 'last seen' showing activity at times you weren't using the app
- Friends receiving messages 'from you' that you didn't send
- Modded WhatsApp installed instead of the official version (check signing certificate)
- Unexpected SMS containing a 6-digit WhatsApp code (someone is trying to take over)
Our WhatsApp Spyware Detection Methodology
Detection is a layered process. We start with the easiest, fastest signals and only escalate to invasive forensics if those come up clean and the user's concern is still substantiated.
Layer 1 — linked-device audit. The first thirty seconds of every engagement. We screenshot the current Linked Devices list, log everything out, and ask the user to verify each device against their actual hardware. Roughly 30% of cases stop here because the 'spyware' was an old WhatsApp Web session never logged out.
Layer 2 — install integrity. We verify the WhatsApp APK signature on Android (com.whatsapp must be signed by 38a0f7d505fe18fec64fbf343ecaaaf310dbd799) or check the App Store install receipt on iOS. A modded WhatsApp will fail this check immediately.
Layer 3 — device forensic acquisition. Encrypted backup pull, MVT scan against current Pegasus and Predator IOC sets, KnowledgeC analysis on iOS or Accessibility-service audit on Android. This catches the device-level spyware that no amount of WhatsApp-only investigation could find.
Layer 4 — backup-side audit. We check whether the iCloud or Google Drive WhatsApp backup has been downloaded by an unfamiliar device. Cloud backups are encrypted but historically have been a soft target where law enforcement and stalkers have obtained content by compromising the cloud account rather than the device.
# Verify the WhatsApp APK signature on Android $ adb shell pm list packages -f | grep whatsapp $ adb shell pm dump com.whatsapp | grep -A1 'Signing certificate' # Expected SHA-256: 38:A0:F7:D5:05:FE:18:FE:C6:4F:BF:34:3E:CA:AA:F3:10:DB:D7:99:9B:6F:7E:71:5C:79:CC:F8:5F:21:8F:7A # Pull WhatsApp's encrypted DB for offline forensic analysis (with consent) $ adb backup -f wa.ab -noapk com.whatsapp $ ./abe.jar unpack wa.ab wa.tar $ tar -xf wa.tar apps/com.whatsapp/db/msgstore.db.crypt15 # On iOS — extract WhatsApp's container from an encrypted backup $ mvt-ios extract-key --backup ./Backup/ --output ./key.bin $ ./mhf-wa-decrypt --backup ./Backup/ --container net.whatsapp.WhatsApp --out wa_messages.json
Myths We Have to Debunk in Almost Every Case
Public discourse about WhatsApp spying is flooded with bad information. These are the four myths we end up correcting in roughly nine out of ten consultations.
Myth 1 — 'Two ticks means someone read it on another device.' False. Two grey ticks means delivered; two blue ticks means read by the recipient on any of their linked devices. Neither indicates spyware.
Myth 2 — 'A WhatsApp call from an unknown number installed Pegasus.' This was true for CVE-2019-3568 in 2019. It was patched within days. A modern unsolicited WhatsApp call cannot install spyware on its own; you would need an unpatched device plus a still-unknown zero-day.
Myth 3 — 'If I delete WhatsApp the spyware goes away.' False if the spyware is at the OS level (Pegasus, stalkerware). The implant continues regardless of which messaging app you use.
Myth 4 — 'End-to-end encryption means nobody can ever read my messages.' True for messages in transit. False for messages on the screen, in the local SQLite database, or in your unencrypted Google Drive backup.
Hands-On Tutorial: 5-Minute WhatsApp Self-Audit
Run this every month. Two-minute commitment, very high signal.
- WhatsApp → Settings → Linked Devices → log out anything not currently in your hand
- Settings → Account → Two-step verification → enable with a 6-digit PIN and a recovery email you control
- Verify the APK signature (Android) or App Store receipt (iOS) for WhatsApp itself
- Settings → Chats → Chat backup → set 'Include videos' OFF and 'End-to-end encrypted backup' ON with a 64-character password
- Settings → Account → Request account info → review the report when it arrives 72h later for unfamiliar device IDs
- Settings → Privacy → 'Last seen and online' → set to 'My contacts' minimum
- If you suspect SIM-swap risk, set up a carrier port-out PIN with your mobile provider
# Self-check on Android — confirm only the official WhatsApp is installed $ adb shell pm list packages | grep -iE 'whatsapp|wa\.' # Anything other than 'com.whatsapp' (and possibly 'com.whatsapp.w4b' for Business) is suspicious # Confirm no Accessibility services are reading WhatsApp's screen $ adb shell settings get secure enabled_accessibility_services # Each entry should be a service you explicitly enabled # Quick check on iOS — list profiles that could be hijacking WhatsApp's traffic # Settings → General → VPN & Device Management — should be EMPTY for personal devices
After the Scan: Hardening WhatsApp Against Future Surveillance
Detection is half the work. The other half is changing the environment so detection isn't necessary again next quarter.
Enable the 64-character end-to-end encrypted backup password. Without it, your iCloud or Google Drive WhatsApp backup is decryptable by anyone who compromises the cloud account. With it, even Apple, Google and WhatsApp themselves cannot read the backup. Store the password in a password manager that itself uses hardware-key 2FA.
Set a port-out PIN with your mobile carrier. This is the single most effective defence against SIM-swap-driven WhatsApp account hijack. Most carriers offer it as a free service on request; we will draft the email script for you.
Limit Linked Devices to one secondary at a time. The multi-device architecture allows four; for high-risk users we recommend one — your primary laptop — and re-linking on the rare occasion you need a second.
On iOS, enable Lockdown Mode. It removes link previews and limits attachment processing, neutralising the historical zero-click WhatsApp vectors that depended on parser bugs in image and PDF handlers.
Frequently Asked Questions
Related Recovery Services
$ Open a secure channel. PGP preferred. Pre-engagement NDA available on request. Ready to proceed?
[ INITIATE SECURE CONTACT ]