Two vulnerabilities in the Galaxy App Store, Samsung’s official repository for its devices, could enable attackers to install any app in the Galaxy Store without the user’s knowledge or to direct victims to a malicious web location.
The issues were discovered by researchers from the NCC Group between November 23 and December 3, 2022.
The Korean smartphone maker announced on January 1, 2023 that it fixed the two flaws and released a new version for Galaxy App Store (4.5.49.8).
Today, the NCC Group published technical details for the two security issues, along with proof-of-concept (PoC) exploit code for each of them.
It should be noted that both attacks require local access, an easy feat for motivated hackers and malware distributors targeting mobile devices.
Forcing app installs on Android
The first of the two flaws is tracked as CVE-2023-21433 and is an improper access control that allows attackers to install any applications available on the Galaxy App Store.
NCC discovered that the Galaxy App Store does not handle incoming intents in a safe way, allowing apps on the device to send arbitrary app installation requests.
The PoC shared by NCC’s analysts is an ‘ADB’ (Android Debug Bridge) command that instructs an app component to install the “Pokemon Go” game by sending an intent with the specified target application to the app store.
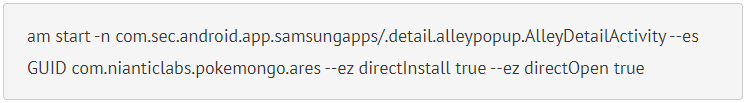
The intent may also specify if the new application should be opened or not after its installation, which gives threat actors more choices over how to conduct the attack.
The second vulnerability is CVE-2023-21434 is an improper input validation that lets attackers execute JavaScript on the target device.
NCC’s researchers found that webviews in the Galaxy App Store contain a filter that limits the domains it can be shown in it. However, that filter isn’t properly configured and can be bypassed to force the webview to access malicious domains.
The PoC presented in the report is a hyperlink that, if clicked from Chrome, will open a page containing malicious JavaScript and run it on the device.
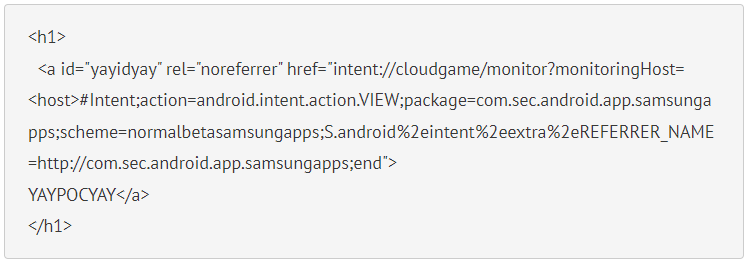
NCC explains that the only prerequisite for this attack is for the malicious domain to have the “player.glb.samsung-gamelauncher.com” part in it. An attacker can register any domain and add that part as a subdomain.
Impact on Samsung users
Running arbitrary JavaScript code in webviews from within system-privilege apps like the Galaxy Store can come with severe security repercussions.
Depending on the attacker’s motives, the attack may lead to app UI interaction, access to sensitive information, or crashing apps.
The installation and automatic launch of apps from the Galaxy Store without the user’s knowledge may also lead to data or privacy breaches, especially if the attacker uploads a malicious app on the Galaxy Store beforehand.
It is important to note that CVE-2023-21433 is not exploitable on Samsung devices running Android 13, even if they use an older and vulnerable version of the Galaxy Store. This is owed to additional security protections on the latest version of Google’s mobile OS.
Unfortunately, all Samsung devices that are no longer supported by the vendor and which remain stuck to an older Galaxy Store version are vulnerable to the two vulnerabilities discovered by the NCC Group researchers.