Multiple platform certificates used by Android OEM device vendors to digitally sign core system applications were utilized by threat actors to sign apps containing malware.
OEM Android device manufacturers use platform certificates, or platform keys, to sign devices’ core ROM images containing the Android operating system and associated apps.
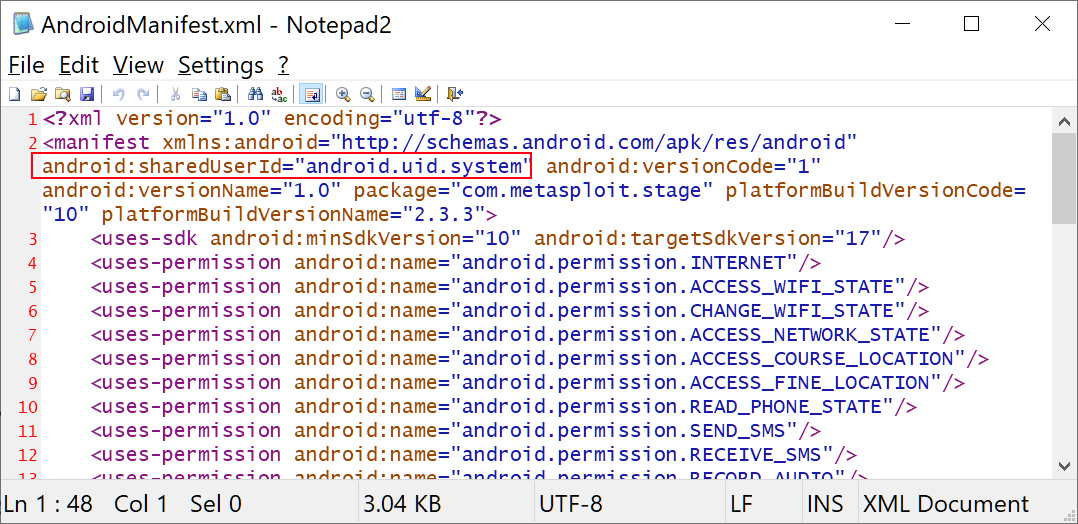
If apps, even malicious ones, are signed with the same platform certificate and assigned the highly privileged ‘android.uid.system’ user id, these apps will also gain system-level access to the Android device.
Source: BleepingComputer
These privileges provide access to sensitive permissions not normally granted to apps, such as managing ongoing calls, installing or deleting packages, gathering information about the device, and other highly sensitive actions.
As shared in a now public report on the Android Partner Vulnerability Initiative (AVPI) issue tracker, this abusive use of platform keys was discovered by Łukasz Siewierski, a Reverse Engineer on Google’s Android Security team.
“A platform certificate is the application signing certificate used to sign the “android” application on the system image. The “android” application runs with a highly privileged user id – android.uid.system – and holds system permissions, including permissions to access user data,” the Google reporter explains.
“Any other application signed with the same certificate can declare that it wants to run with the same user id, giving it the same level of access to the Android operating system.”
Siewierski spotted multiple malware samples signed using these ten Android platform certificates and provided the SHA256 hashes for each of the samples and the digitally signed certificates.
At the moment, there is no information on what led to these certificates being abused to sign malware — if one or more threat actors stole them or if an insider with authorized access signed the APKs with the vendor keys.
Also, there is no information on where these malware samples were found — if they were found on Google’s Play Store or if they’ve been distributed via third-party stores or in malicious attacks.
The package names for the ten listed malware samples signed with platform keys are listed below:
com.russian.signato.renewis
com.sledsdffsjkh.Search
com.android.power
com.management.propaganda
com.sec.android.musicplayer
com.houla.quicken
com.attd.da
com.arlo.fappx
com.metasploit.stage
com.vantage.ectronic.cornmuniLeaked certs belong to Samsung, LG, Revoview, and MediaTek
A search on VirusTotal for these hashes allowed BleepingComputer to discover that some of the abused platform certificates belong to Samsung Electronics, LG Electronics, Revoview, and Mediatek.
For the other certificates, it was not possible to determine who they belonged to at this time.
Malware signed with their certificates includes those detected as HiddenAd trojans, information stealers, Metasploit, and malware droppers that threat actors can use to deliver additional malicious payloads on compromised devices.
Google informed all affected vendors about the abuse and advised them to rotate their platform certificates, investigate the leak to find out how it happened, and keep the number of apps signed with their Android platform certs at a minimum to prevent future incidents.
“All affected parties should rotate the platform certificate by replacing it with a new set of public and private keys. Additionally, they should conduct an internal investigation to find the root cause of the problem and take steps to prevent the incident from happening in the future,” the Google reporter added.
“We also strongly recommend minimizing the number of applications signed with the platform certificate, as it will significantly lower the cost of rotating platform keys should a similar incident occur in the future.”
An easy way to get an overview of all Android apps signed with these potentially compromised certificates is to use APKMirror to search for them (a list of apps signed with Samsung’s cert and one of the LG-signed apps).
However, based on the results, even though Google said that “all affected parties were informed of the findings and have taken remediation measures to minimize the user impact,” it looks like not all the vendors have followed Google’s recommendations since, at least in Samsung’s case, the leaked platform certificates are still being used to digitally sign apps.
When we reached out to Google about these compromised keys, Google told BleepingComputer that they had added detections for the compromised keys to the Android Build Test Suite (BTS) and malware detections to Google Play Protect.
“OEM partners promptly implemented mitigation measures as soon as we reported the key compromise. End users will be protected by user mitigations implemented by OEM partners,” Google said in a statement to BleepingComputer.
“Google has implemented broad detections for the malware in Build Test Suite, which scans system images. Google Play Protect also detects the malware.”
“There is no indication that this malware is or was on the Google Play Store. As always, we advise users to ensure they are running the latest version of Android.”