
The Russian hacking group known as ‘Nodaria’ (UAC-0056) is using a new information-stealing malware called ‘Graphiron’ to steal data from Ukrainian organizations.
The Go-based malware can harvest a wide range of information, including account credentials, system, and app data. The malware will also capture screenshots and exfiltrate files from compromised machines.
Symantec’s threat research team discovered that Nodaria has been using Graphiron in attacks since at least October 2022 through mid-January 2023.
Stealing sensitive information
Graphiron consists of a downloader and a secondary information-stealing payload.
When launched, the downloader will check for various security software and malware analysis tools, and if none are detected, download the information-stealing component.
Some of the processes the downloader checks for include BurpSuite, Charles, Fiddler, rpcapd, smsniff, Wireshark, x96dbg, ollydbg, and idag.
The malware uses names such as OfficeTemplate.exe and MicrosoftOfficeDashboard.exe to masquerade as a Microsoft Office component on the breached system.
Its capabilities include the following:
- Read MachineGuid
- Obtain the IP address from https://checkip.amazonaws.com
- Retrieve the hostname, system info, and user info
- Steal data from Firefox and Thunderbird
- Steal private keys from MobaXTerm.
- Steal SSH known hosts
- Steal data from PuTTY
- Steal stored passwords
- Take screenshots
- Create a directory
- List a directory
- Run a shell command
- Steal an arbitrary file
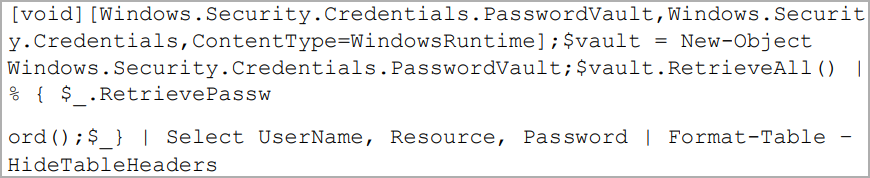
The malware uses the following PowerShell code to steal passwords from the Windows Vault, the system’s built-in password manager, where saved credentials are stored in AES-256 encrypted form.
Graphiron uses AES encryption with hardcoded keys to communicate with the C2 server through port 443, a noteworthy similarity to older Nodaria tools like GraphSteal and GrimPlant.
Nodaria targeting Ukraine
Nodaria is the same threat actor that deployed a fake ransomware named ‘WhisperGate‘ on Ukrainian networks in January 2022, performing destructive data-wiping attacks.
Typically, Russian hackers deliver their payloads to targets via spear-phishing emails, with the ongoing war providing plenty of opportunity for effective baits.
Graphiron is the latest addition to Nodaria’s arsenal, combining the features of the group’s past custom tools into one payload while also featuring obfuscation.
This is a sign that Nodaria will continue to target Ukrainian organizations, attempting to collect valuable information from high-profile targets.



