
The Play ransomware operation has claimed responsibility for a recent cyberattack on the Belgium city of Antwerp.
Last week, Digipolis, the IT company responsible for managing Antwerp’s IT systems, suffered a ransomware attack that disrupted the city’s IT, email, and phone services.
Local media reported that many of the city’s Windows applications were no longer available, and City council member Alexandra d’Archambeau publicly tweeted that email was not available.
The disruption continues with the city warning that almost all services are unavailable or significantly delayed, including job applications, use of libraries, and new agreements with the city.
Play ransomware claims attack
While local media had confirmed that ransomware was behind the attack, it was unclear what operation attacked the city.
Over the weekend, Emsisoft threat analyst Brett Callow noticed that the Play ransomware operation started listing Antwerp as one of its victims.
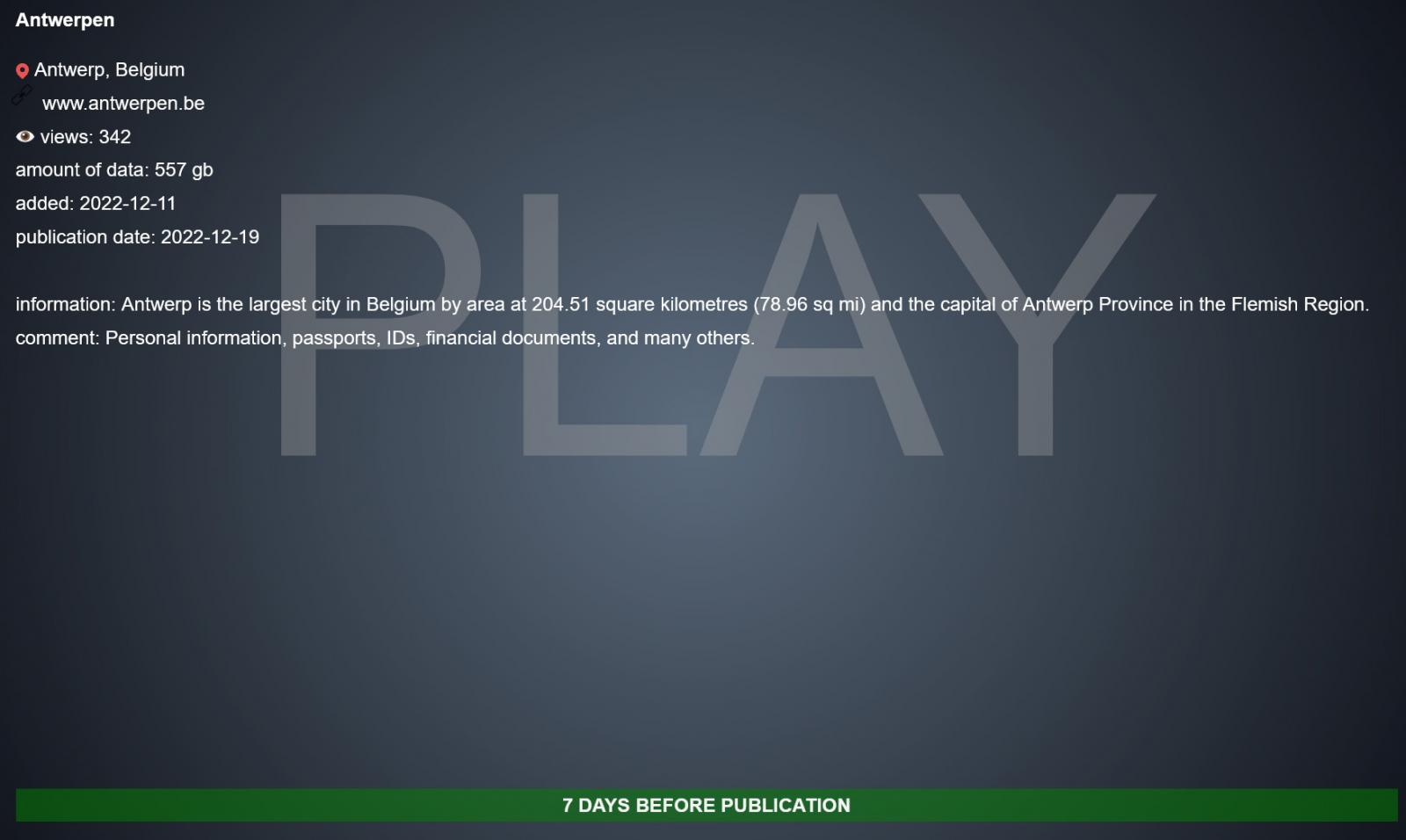
This Antwerp entry on the data leak site claims that 557 GB of data was stolen during the attack, including personal information, passports, IDs, and financial documents.
Source: BleepingComputer
However, data from the city has yet to be leaked, with the threat actors indicating they will begin publishing data in a week unless a ransom is paid.
Play ransomware is a relatively new operation, launched in June 2022 when victims began describing their attacks in the BleepingComputer forums.
Soon after, the ransomware gang targeted Argentina’s Judiciary of Córdoba, in what was their most significant known attack.
Since then, the ransomware operation has slowly grown, amassing a steady stream of victims worldwide.



