
Over 19,000 end-of-life Cisco VPN routers on the Internet are exposed to attacks targeting a remote command execution exploit chain.
By chaining two security flaws disclosed last week, threat actors can bypass authentication (CVE-2023-20025) and execute arbitrary commands (CVE-2023-2002) on the underlying operating system of Cisco Small Business RV016, RV042, RV042G, and RV082 routers.
Unauthenticated attackers can exploit the critical severity auth bypass flaw remotely via specially crafted HTTP requests sent to the vulnerable routers’ web-based management interface to gain root access.
Cisco rated CVE-2023-20025 as critical and said that its Product Security Incident Response Team (PSIRT) team is aware of proof-of-concept exploit code available in the wild.
Despite this, the company also said it “has not and will not release software updates that address this vulnerability.”
For the time being, Cisco has found no evidence suggesting that this exploit chain is being abused in attacks.
Thousands of routers vulnerable to attacks
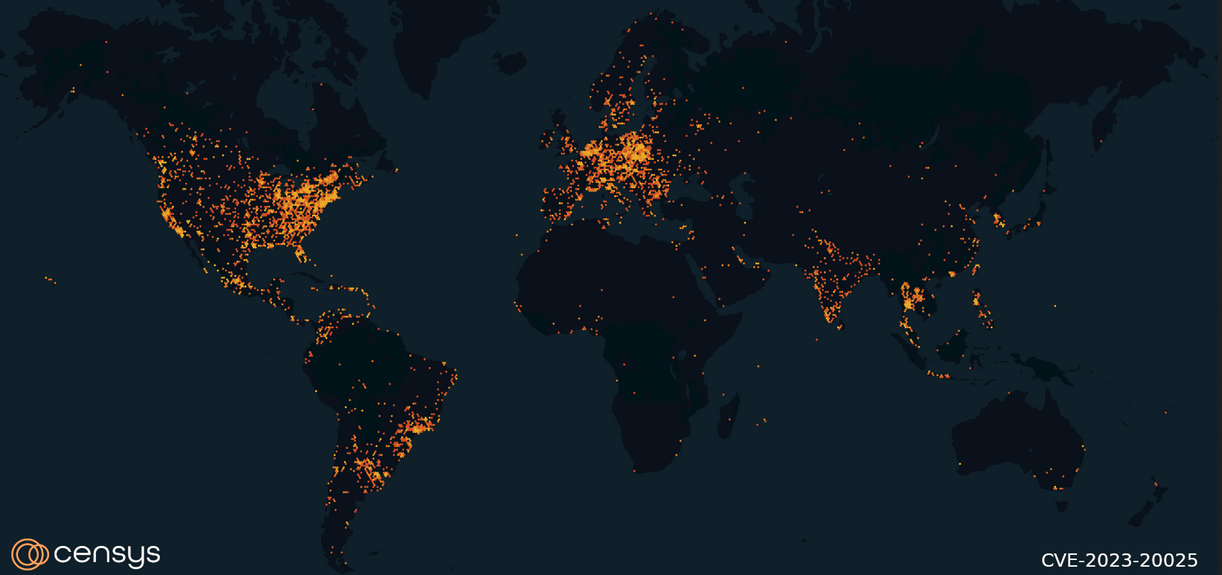
After BleepingComputer reported that these routers would be left without a patch and looking into how many of them are reachable over the Internet, Censys found almost 20,000 RV016, RV042, RV042G, and RV082 Cisco routers online.
“By looking at only HTTP services that include the model numbers in either the ‘WWW-Authenticate’ response header or an HTTPS service with a matching TLS organizational unit, Censys search results show around 20,000 hosts have indicators that they are potentially vulnerable to this attack,” Censys said.
“Of the four vulnerable models, the RV042 dominates the landscape, with over 12k hosts exposed to the internet.
“The RV082 and RV042 with 3.5k hosts, while the RV016 trails behind with only 784 internet-exposed assets.”
Although they won’t get security updates, and Cisco said that there “are no workarounds that address these vulnerabilities,” users can still secure their devices from attacks by disabling the web-based management interface and blocking access to ports 443 and 60443 to thwart exploitation attempts.
To do that, log into each vulnerable router’s web-based management interface, go to Firewall > General, and uncheck the Remote Management check box. Cisco also provides detailed instructions on blocking access to ports 443 and 60443.
The affected routers will still be accessible and can be configured via the LAN interface after implementing the above mitigation.
Cisco also said it wouldn’t fix a critical auth bypass flaw affecting multiple EoL routers in September and advised users to switch to RV132W, RV160, or RV160W routers still under support.
Three months earlier, in June, Cisco again encouraged owners to migrate to newer router models after disclosing a critical remote code execution (RCE) vulnerability in another series of end-of-life VPN routers that was also left unpatched.



