
Many online stores are exposing private backups in public folders, including internal account passwords, which can be leveraged to take over the e-commerce sites and extort owners.
According to a study by website security company Sansec, roughly 12% of online stores forget their backups in public folders due to human error or negligence.
The study examined 2,037 stores of various sizes and found that 250 (12.3%) exposed ZIP, SQL, and TAR archives on public web folders that can be freely accessed without requiring authentication.
The archives appear to be backups containing database passwords, secret administrator URLs, internal API keys, and customer PII (personally identifiable information).

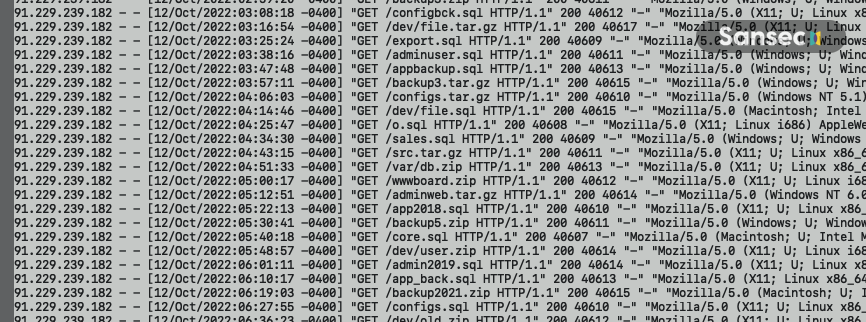
In the same report, Sansec explains that its analysts observe constant activity from attackers who launch automated scans trying to pinpoint these backups and perform breaches.
“Online criminals are actively scanning for these backups, as they contain passwords and other sensitive information,” reads the Sansec report.
“Exposed secrets have been used to gain control of stores, extort merchants and intercept customer payments.”
Threat actors try out various combinations of possible backup names on target sites based on the site name and public DNS data, such as “/db/staging-SITENAME.zip.”
Because these probes are inexpensive to run and do not affect the target store’s performance, threat actors can conduct them for entire weeks until they find a backup.
Sansec reports seeing multiple source IPs for these attacks, so threat actors are well aware of the existence of exposed backups, and many of them are attempting to take advantage.
If the exposed backups contain administrator details, master database passwords, or staff accounts, the attackers can use them to gain access to the site and steal data or perform destructive attacks.
Check your sites!
Sansec urges website owners to routinely check their sites for accidentally exposed data and backup.
If you have exposed a website backup publicly, immediately reset admin accounts and database passwords, and enable 2FA on all staff accounts.
Additionally, check the web server logs to see if the backup was downloaded by a third party, and check admin account activity logs to identify signs of external access and malicious behavior.
Sansec suggests that website administrators configure the webserver to restrict access to archive files if not needed in daily operations to prevent data leaks.
Additionally, those using the Adobe Commerce platform should use the “immutable storage” feature.



