
A new information stealer called Stealc has emerged on the dark web gaining traction due to aggressive promotion of stealing capabilities and similarities with malware of the same kind like Vidar, Raccoon, Mars, and Redline.
Security researchers at cyber threat intelligence company SEKOIA spotted the new strain in January and noticed it started to gain tractionin early February.
New stealer for sale
Stealc has been advertised on hacking forums by a user called “Plymouth,” who presented the malware as a piece of malware with extensive data-stealing capabilities and an easy-to-use administration panel.
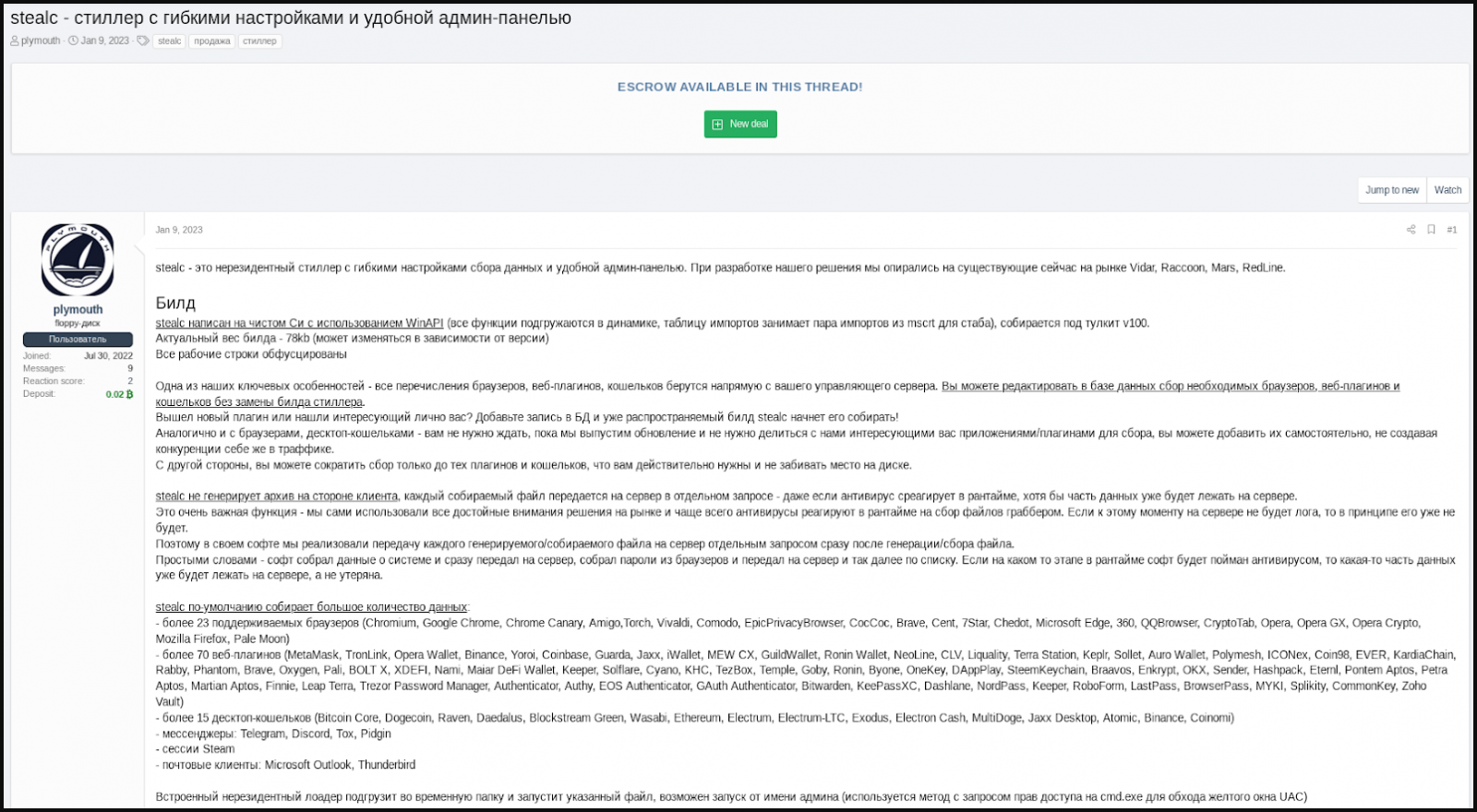
According to the advertiser, apart from the typical targeting of web browser data, extensions, and cryptocurrency wallets, Stealc also has a customizable file grabber that can be set to target whatever file types the operator wishes to steal.
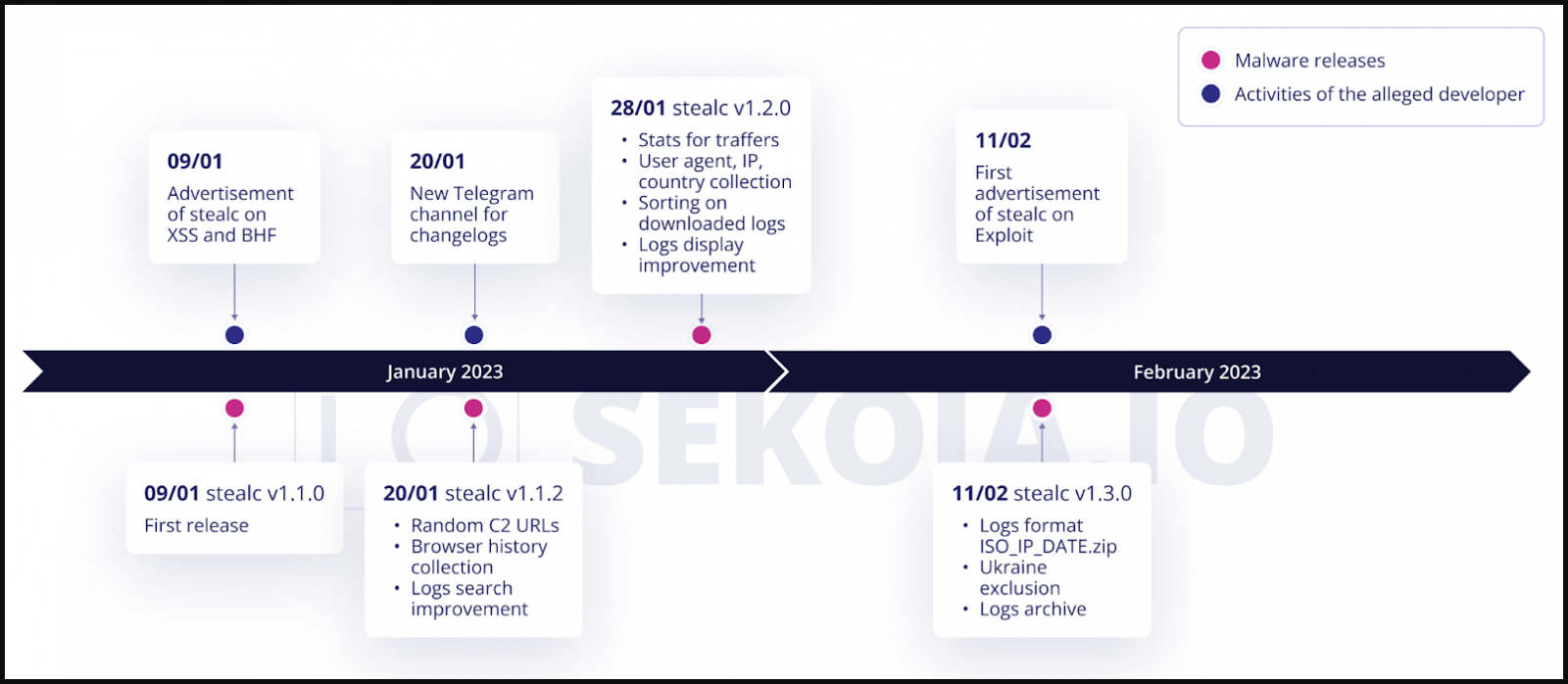
After the initial post, Plymouth started to promote the malware on other hacking forums and on private Telegram channels, offering test samples to potential customers.
The seller also set up a Telegram channel dedicated to publishing Stealc’s new version changelogs, the most recent being v1.3.0, released on February 11, 2023. The malware is actively developed, and a new version appears on the channel every week.
Plymouth also said that Stealc was not developed from scratch but instead relied on Vidar, Raccoon, Mars and Redline stealers.
One commonality the researchers found between Stealc and Vidar, Raccoon and Mars infostealers is that they all download legitimate third-party DLLs (e.g. sqlite3.dll, nss3.dll) to help with pilfering sensitive data.
In a report today, SEKOIA researchers note that the command and control (C2) communications of one of the samples they analyzed shared similarities to those of Vidar and Raccoon info stealers.
The researchers discovered more than 40 C2 servers for Stealc and several dozens of samples in the wild, indicating that the new malware has attracted the interest of the cybercriminal community.
This popularity may be accounted by the fact that customers with access to the administration panel can generate new stealer samples, which increase the chances of the malware leaking to a broader audience.
Despite the poor business model, SEKOIA believes that Stealc represents a significant threat as it could be adopted by less technical cybercriminals.
Stealc’s functions
Stealc has added new features since its first release in January, including a system to randomize C2 URLs, a better logs (stolen files) searching and sorting system, and an exclusion for victims in Ukraine.
The features that SEKOIA could verify by analyzing the captured sample are the following:
- Lightweight build of only 80KB
- Use of legitimate third-party DLLs
- Written in C and abusing Windows API functions
- Most strings are obfuscated with RC4 and base64
- The malware exfiltrates stolen data automatically
- It targets 22 web browsers, 75 plugins, and 25 desktop wallets
SEKOIA’s curent report does not include all the data obtained from reverse engineering Stealc but provides an overview of the main steps of its execution.
When deployed, the malware deobfuscates its strings and performs anti-analysis checks to ensure it doesn’t run in a virtual environment or sandbox.
Next, it dynamically loads WinAPI functions and initiates communication with the C2 server, sending the victim’s hardware identifier and build name in the first message, and receiving a configuration in response.
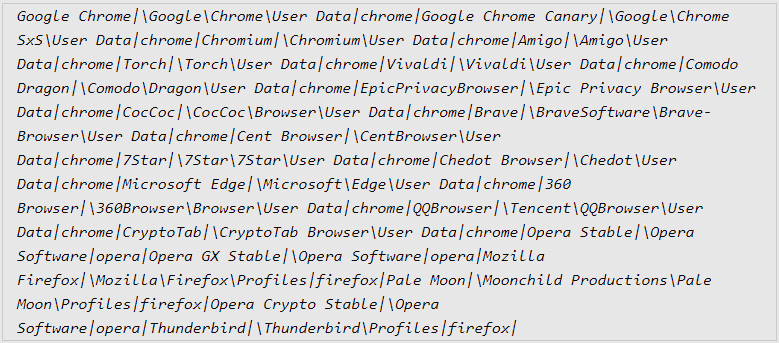
Stealc then collects data from the targeted browsers, extensions, and apps, and also executes its custom file grabber if active, and finally exfiltrates everything to the C2. Once this step is over, the malware removes itself and the downloaded DLL files from the compromised host to wipe the traces of the infection.
For the complete list of Stealc’s capabilities and targeted apps, check out the Annex 1 section in SEKOIA’s report.
One distribution method the researchers observed is via YouTube videos describing how to install cracked software and linking to a download website.
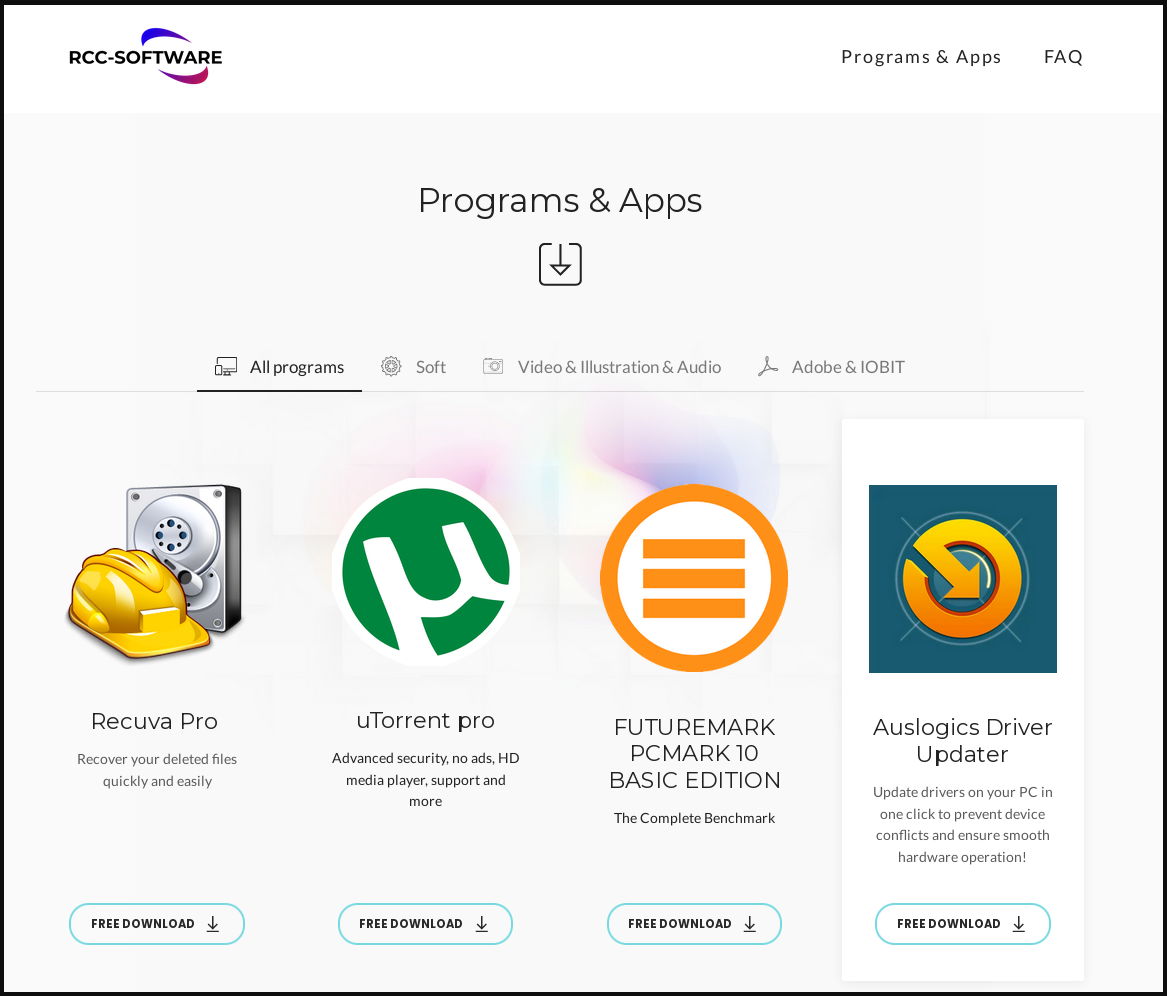
The researchers say that the software download embeds the Stealc info stealer. Once the installer is executed, the malware begins its routine and communicates with its server.
SEKOIA has shared a large set of indicators of compromise that companies can use to defend their digital assets as well as YARA and Suricata rules to detect the malware based on decryption routine, specific strings and behavior,
Considering the observed distribution method, users are recommended to steer away from installing pirated software and download products only from the official developer’s website.



