
Microsoft announced that it will retire Microsoft Support Diagnostic Tool (MSDT) troubleshooters in future versions of Windows, with MSDT ultimately being removed in 2025.
Also known as legacy inbox troubleshooters, these Windows built-in tools are used to diagnose and fix issues affecting some Windows features automatically.
While the MSDT app that runs them will be retired in 2025, the troubleshooters will be killed off with the launch of the next Windows 11 release.
After being retired, some MSDT troubleshooters will be redirected to Microsoft’s Get Help platform (starting later this year), while the remaining ones will be removed.
You can access the Get Help troubleshooters from Windows Settings by going to Start > Settings > System > Troubleshoot > Other Troubleshooters and selecting the troubleshooter that would help you address your issues.
According to Redmond’s estimated deprecation timeline, the MSDT deprecation process will be done in stages over the next three years:
- 2023 – Begin redirecting some of the troubleshooters to the new Get Help troubleshooting platform
- 2024 – Complete the troubleshooter redirection and remove the rest of the troubleshooters
- 2025 – Remove the MSDT platform
“If you’re running Windows 11 version 22H2 and older, Windows 10, Windows 8.1, Windows 7 or any other earlier OS version, your device will not be affected by the MSDT Troubleshooter retirement,” Microsoft added.
This is because the legacy inbox troubleshooters will continue to work as expected on earlier Windows OS versions until they’re upgraded or updated to the latest release.
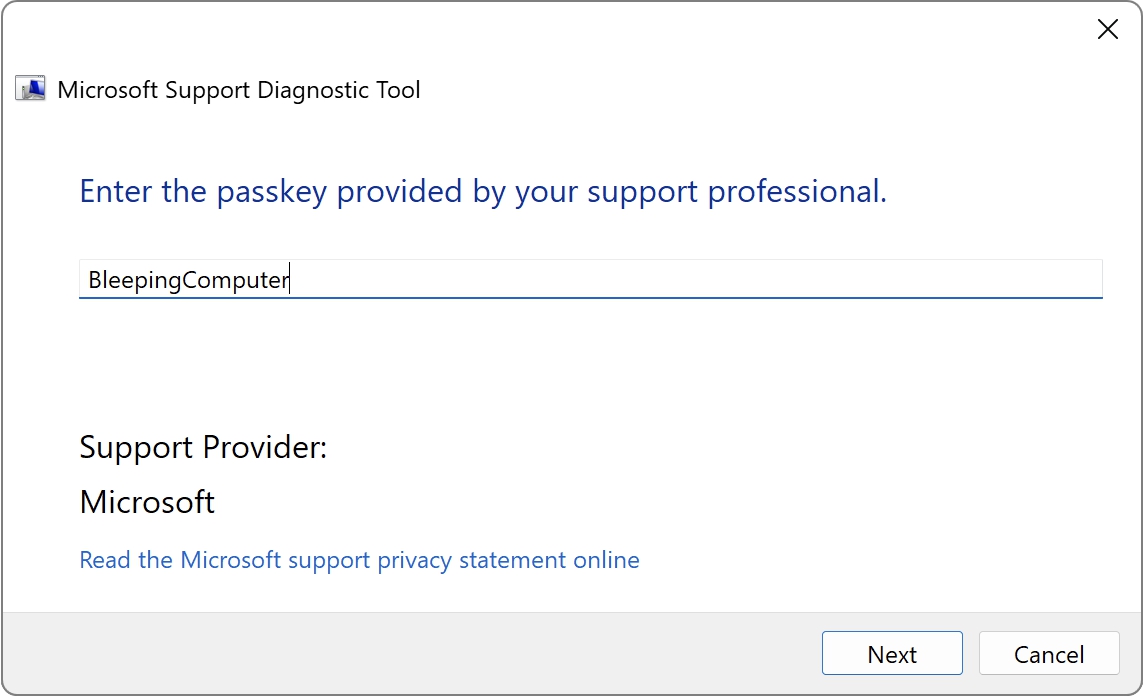
This week’s announcement comes after Microsoft temporarily displayed a retirement message within MSDT’s user interface in January 2023.
Likely retired because of security issues
While Redmond doesn’t explain the reasons behind deprecating MSDT in future Windows versions, a possible explanation would be MSDT vulnerabilities patched by Microsoft in 2022 after they were exploited in the wild using zero-day exploits.
Both the DogWalk (CVE-2022-34713) and the Follina (CVE-2022-30190) vulnerabilities allow unauthenticated attackers to gain remote code execution on unpatched Windows systems in low-complexity attacks.
“A remote code execution vulnerability exists when MSDT is called using the URL protocol from a calling application such as Word. An attacker who successfully exploits this vulnerability can run arbitrary code with the privileges of the calling application,” Microsoft said when describing the Follina bug.
“The attacker can then install programs, view, change, or delete data, or create new accounts in the context allowed by the user’s rights.”
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added the two security flaws to its catalog of Known Exploited Vulnerabilities and ordered federal agencies to patch them as soon as possible to thwart incoming attack attempts.



