
Microsoft is working on adding XLL add-in protection for Microsoft 365 customers by including automated blocking of all such files downloaded from the Internet.
This will help tackle the rise of malware campaigns abusing this infection vector to an ever-growing extent during the last several years.
“In order to combat the increasing number of malware attacks in recent months, we are implementing measures that will block XLL add-ins coming from the internet,” Redmond says.
Microsoft says the new feature will reach general availability in multi-tenants worldwide in March for desktop users in the Current, Monthly Enterprise, and Semi-Annual Enterprise channels.
Attackers are using XLL add-ins (Excel DLLs) in phishing campaigns to push various malicious payloads in the form of download links or attachments camouflaged as documents from trusted entities such as business partners or as fake advertising requests, holiday gift guides, and website promotions.
Once the target double clicks on an unsigned XLL file to open it, they will be warned of “a potential security content,” that “add-ins might contain viruses or other security hazards,” and prompted to enable the add-in for the current session.
If the add-in is activated (and many people ignore Office alerts without giving them a second glance), it will also deploy a malware payload on the victim’s device in the background.
As XLL files are executables and attackers can use them for various malicious tasks, you must only open one if you’re 100% sure it comes from a trusted source.
Additionally, such files are not generally sent as email attachments but instead installed by a Windows admin. Therefore, if you receive an email or any other message pushing such files, delete the message and report it as spam.

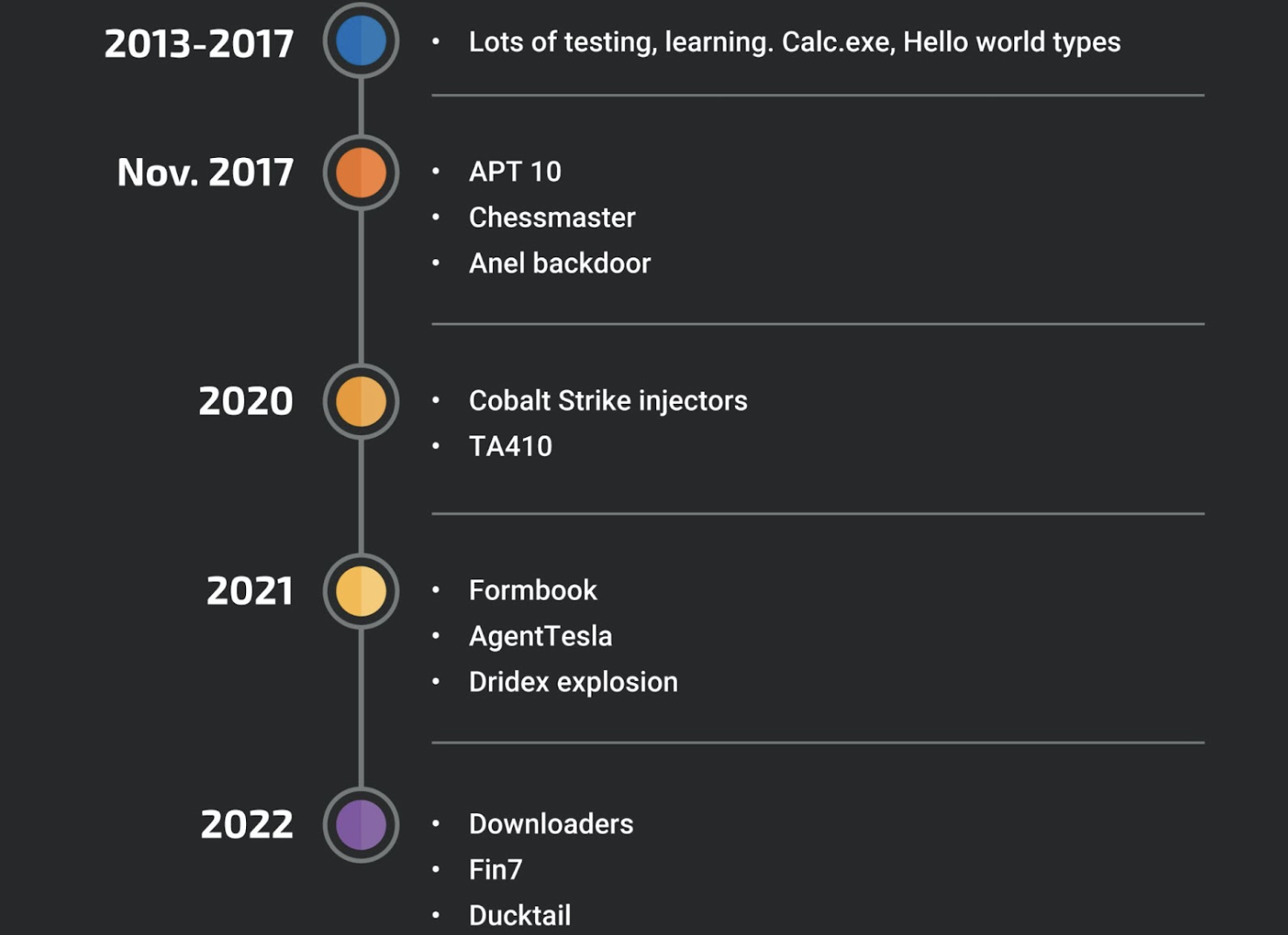
As Cisco Talos said in a January report, XLLs are now used by both financially-motivated attackers and state-backed threat groups (APT10, FIN7, Donot, TA410) as an infection vector to deliver first-stage payloads onto their targets’ devices.
“Even if XLL add-ins existed for some time, we were not able to detect their usage by malicious actors until mid-2017 when some APT groups started using them to implement a fully functional backdoor,” Cisco Talos said.
“We also identified that their usage significantly increased over the last two years as more commodity malware families adopted XLLs as their infection vector.”
One year ago, HP’s threat analyst team reported seeing a “near-sixfold surge in attackers using Excel add-ins (.XLL)” as part of its Threat Insights Report Q4 2021.
This is part of a broader effort to block threat actors from using malicious Office documents to deliver and install malware on their targets’ computers.
Since July 2022, Microsoft said Office VBA macros would be auto-blocked in downloaded Office documents, making it harder to enable in docs downloaded from the Internet in several Office apps (Access, Excel, PowerPoint, Visio, and Word).
In March 2021, the company added XLM macro protection in M365 by expanding the runtime defense provided by Office 365’s integration with Antimalware Scan Interface (AMSI) to include Excel 4.0 (XLM) macro scanning.
Redmond started disabling Excel 4.0 (XLM) macros by default when opened in Microsoft 365 tenants in January 2021.
Years before, in 2018, Microsoft also extended support for AMSI to Office 365 apps to defend customers against attacks using VBA macros.



