
Microsoft has disabled multiple fraudulent, verified Microsoft Partner Network accounts for creating malicious OAuth applications that breached organizations’ cloud environments to steal email.
In a joint announcement between Microsoft and Proofpoint, Microsoft says the threat actors posed as legitimate companies to enroll and successfully be verified as that company in the MCPP (Microsoft Cloud Partner Program).
The threat actors used these accounts to register verified OAuth apps in Azure AD for consent phishing attacks targeting corporate users in the UK and Ireland.
Microsoft says the malicious OAuth apps were used to steal customers’ emails. However, Proofpoint warned that the app’s permissions could have allowed them to access calendars and meeting information and modify user permissions.
Typically, this information is used for cyberespionage, BEC (business email compromise) attacks, or to gain further access to internal networks.
Proofpoint disclosed the malicious campaign on December 15, 2022, with Microsoft soon shutting down all fraudulent accounts and OAuth apps.
“Microsoft has disabled the threat actor-owned applications and accounts to protect customers and have engaged our Digital Crimes Unit to identify further actions that may be taken with this particular threat actor,” reads the announcement.
“We have implemented several additional security measures to improve the MCPP vetting process and decrease the risk of similar fraudulent behavior in the future.”
Microsoft has contacted all impacted organizations and warned that they should conduct a thorough internal investigation to verify that the suspicious applications have been disabled from their environment.
BleepingComputer has contacted Microsoft to learn more about the attacks and how they are improving the MCPP vetting process, but a response was not immediately available.
Impersonating legitimate companies
OAuth applications allow third-party applications to gain permission to access the data in a user’s cloud account to perform a specific action, such as generating calendar events or scanning emails for malware.
Instead of logging into an OAuth application with a user’s credentials, they are registered with Azure AD and can be granted requested permissions on a user’s account. These permissions can be easily revoked without changing a user’s credentials if necessary.
Over the past few years, malicious threat actors have used OAuth apps in ‘consent phishing’ attacks to access targeted organizations’ Office 365 and Microsoft 365 cloud data.
To further protect customers, Microsoft allows developers to become verified publishers, meaning Microsoft has verified their identity.
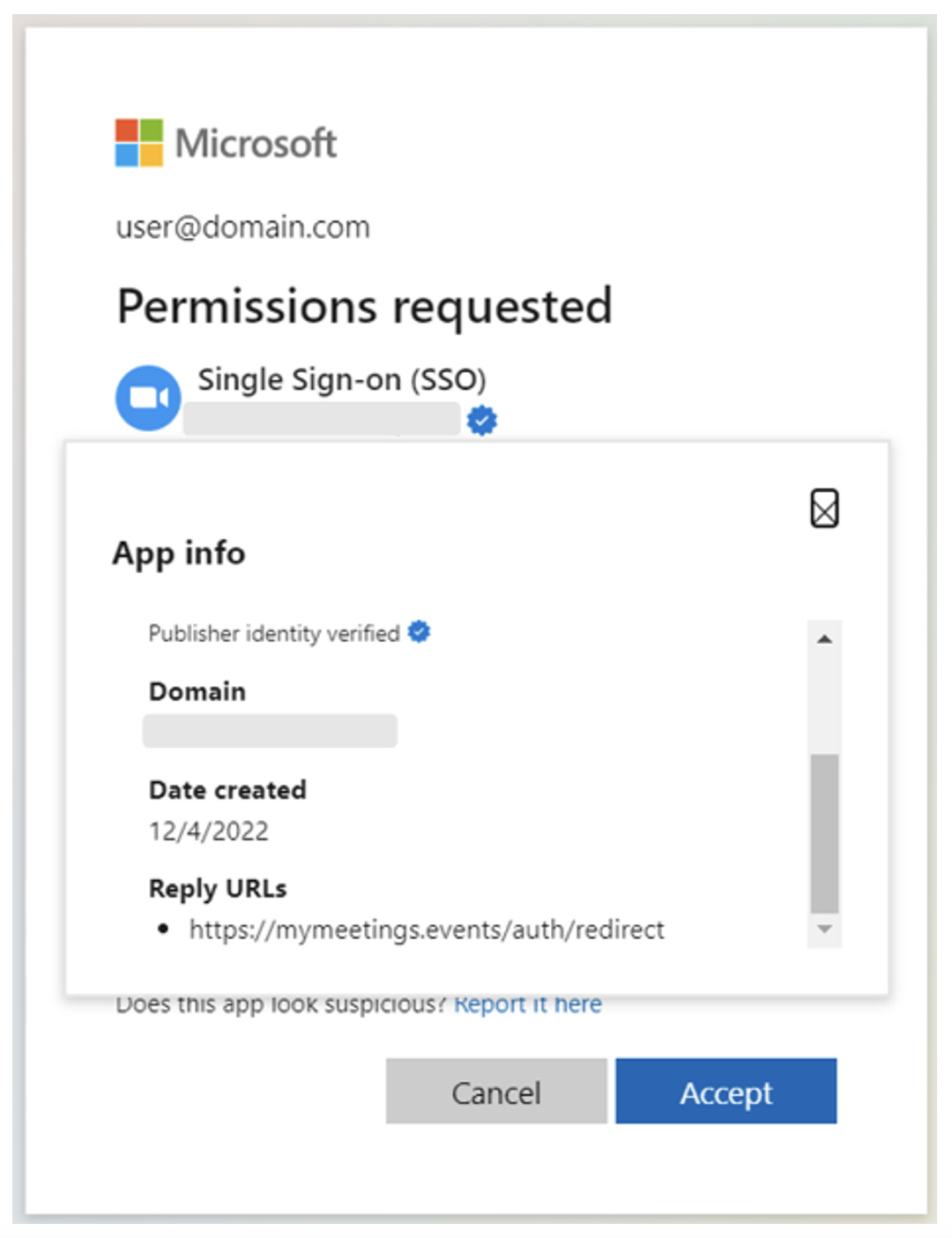
OAuth apps that a verified partner creates have a blue check in the Azure Active Directory (Azure AD) consent prompt, indicating that this application is more trustworthy.
According to a Proofpoint report released today, researchers explained that the threat actors switched from trying to compromise existing Microsoft-verified publisher accounts and instead impersonated credible publishers to become verified themselves.
The threat actors impersonated other companies by using a similar display name to an existing verified publisher but hid the “verified publisher” name, which was different, as changing that would require re-verification with Microsoft.
They also linked to the legitimate company’s “terms of service” and “policy statement” web pages to add further legitimacy to their apps and identity.
Proofpoint identified three malicious OAuth apps from three verified publishers, all targeting the same organizations and communicating with the same attacker-controlled infrastructure.
“According to our analysis, this campaign appeared to target mainly UK-based organizations and users. Among the affected users were financial and marketing personnel, as well as high-profile users such as managers and executives,” says Proofpoint.
Two of the apps were named “Single Sign On (SSO),” and the third one was called “Meeting,” requesting access to the following permissions:
- Read your mail
- Maintain access to data you have given it access to
- Read your mailbox settings
- Sign you in and read your profile
- Send mail as you
- Read your calendars
- Read your online meetings
Unfortunately, Proofpoint saw evidence of multiple users impacted by the attacks, resulting in the compromise of their organizations.
The campaign spanned between December 6, 2022, and December 27, 2022, when Microsoft disabled all malicious applications. The investigation into the attack continues.
In January 2022, we covered a similar campaign discovered by Proofpoint, where threat actors abused previously compromised verified publisher accounts to create trustworthy OAuth apps with which they targeted company executives.
Microsoft has published a detailed guide on how users can protect themselves against these attacks and the recommended practices to prevent them in the first place.



