
Email marketing firm MailChimp suffered another breach after hackers accessed an internal customer support and account administration tool, allowing the threat actors to access the data of 133 customers.
MailChimp says the attackers gained access to employee credentials after conducting a social engineering attack on Mailchimp employees and contractors.
The attack was first detected on January 11th, after MailChimp detected the unauthorized person accessing their support tools.
“After we identified evidence of an unauthorized actor, we temporarily suspended account access for Mailchimp accounts where we detected suspicious activity to protect our users’ data,” reads a statement about the security incident.
“We notified the primary contacts for all affected accounts on January 12, less than 24 hours after initial discovery.”
In response to our questions about the breach, MailChimp shared the following statement.
“While we do not share customer information as a matter of course, we can share that no credit card or password information was compromised as a result of this incident,” MailChimp told BleepingComputer.
“Our investigation into the matter is ongoing, and includes identifying measures to further protect our platform. For operational security reasons we are not publicly commenting on actions we are taking. – MailChimp.
As first reported by TechCrunch, one of the customers affected by this breach is the massively popular WooCommerce eCommerce plugin for WordPress.
WooCommerce has emailed customers warning them that the MailChimp breach exposed their names, store URLs, addresses, and email addresses.
#Woocommerce Users receive this from a noreply email address as an information of a data #breach at #Mailchimp. #privacy #malware #dataprotection #itsecurity pic.twitter.com/O9AmA2cyBu
— Armin (@Arm_i_n) January 18, 2023
While WooCommerce states that there is no indication that the stolen data has been misused, threat actors commonly use this type of data for targeted phishing attacks to steal credentials or install malware.
In April 2022, Trezor hardware wallet owners began receiving fake data breach notifications prompting customers to download a fake Trezor Suite software that would steal their recovery seeds.
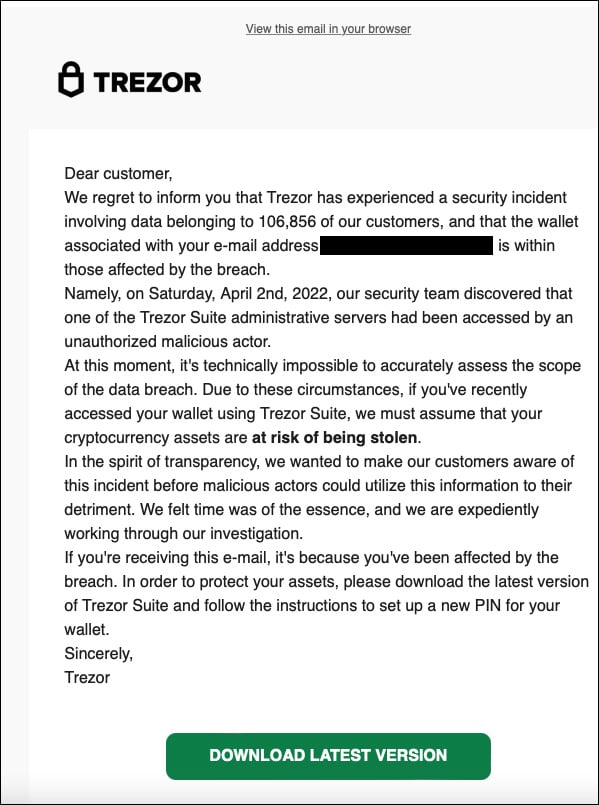
Trezor said on Twitter that the mailing list used in this phishing campaign was a Trezor mailing list stolen in a breach on MailChimp.
MailChimp later confirmed that the breach was more extensive, with employees falling for a social engineering attack that allowed threat actors to access 319 MailChimp accounts and export the data from 102 customers.
The marketing company confirmed that this data was being used in phishing emails but declined to share more information about the attacks.
In August 2022, MailChimp was again breached after employees fell for an Okta phishing attack dubbed ‘0ktapus.’
MailChimp told BleepingComputer at the time that the threat actors accessed 214 MailChimp accounts, focusing on cryptocurrency-related customers.
Customers affected in the August breach included Edge Wallet, Cointelegraph, NFT creators, Ethereum FESP, and Messari and Decrypt.



