
The Clop ransomware gang is now also using a malware variant that explicitly targets Linux servers, but a flaw in the encryption scheme has allowed victims to quietly recover their files for free for months.
This new Linux version of Clop was spotted in December 2022 by Antonis Terefos, a researcher at SentinelLabs, after the threat group used it together with the Windows variant in an attack against a university in Colombia.
While very similar to the Windows version, as they both use the same encryption method and almost identical process logic, there still are some differences, mainly limited to OS API calls and features still waiting to be implemented in the Linux variant.
Clop’s Linux malware is also in early development, as it’s still missing proper obfuscation and evasiveness mechanisms, and it is plagued by flaws that make it possible for victims to retrieve their files without paying the crooks any money.
Targeting Oracle database servers
The Linux executable (ELF) of Clop ransomware creates a new process upon launch, which attempts to elevate permissions to a level that would allow data encryption.
The files and folders it targets include the user’s “/home” directory, which contains all personal files, the “/root” directory, “/opt,” and Oracle directories (“/u01” – “/u04”) used for storing database files or as mount points for Oracle software.
The specific targeting of Oracle database folders is not commonly seen in Linux ransomware encryptors, which usually focus on encrypting ESXi virtual machines.
The Linux variant also lacks support for the hashing algorithm used by the Windows version to exclude certain file types and folders from encryption. Also, there’s no mechanism to treat files of various sizes differently on Linux.
Other features not present in the Linux version of Clop include the absence of drive enumeration, which would help find the starting point for encrypting folders recursively, and command line parameters to provide additional control over the encryption process.
Encryption flaws
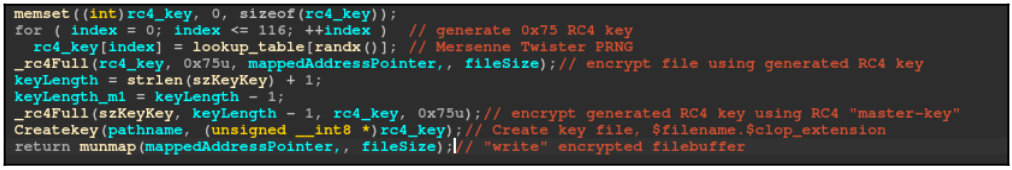
The current Linux version will also not encrypt the RC4 keys used for file encryption with the RSA-based asymmetric algorithm used in the Windows variant.
Instead, in the Linux version, Clop uses a hardcoded RC4 “master key” to generate the encrypting keys and then uses the same key to encrypt it and store it locally on the file. Also, the RC4 key is never validated, whereas, in Windows, it’s validated before initiating the encryption.
This weak scheme does not protect the keys from being freely retrieved and the encryption from being reversed, which SentinelLabs has done (a Python script that does just that is now available on GitHub).
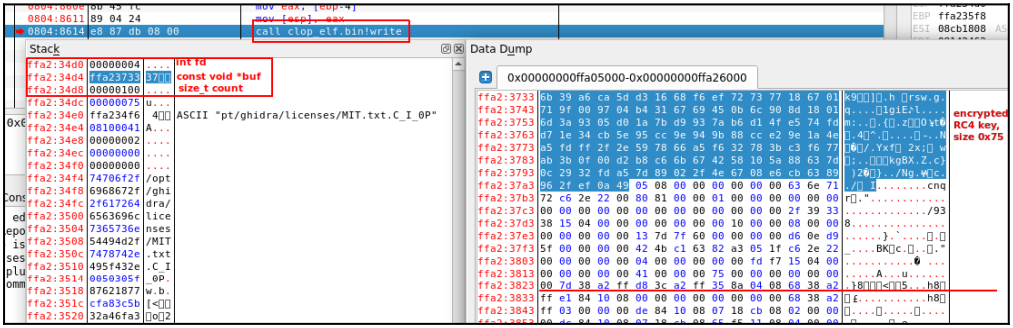
In addition to the lack of key security, SentinelLabs also found that when the encrypted key is written to a file, the malware also writes some extra data, like details about the file, such as its size and time of encryption.
This data should be concealed, as it could help forensic specialists perform targeted decryption of specific, valuable files.
Clop ransomware for Linux is unlikely to become a widespread threat in its current form. The release of a decryptor will likely push its authors to release secure and improved versions with a proper encryption scheme.
SentinelLabs told BleepingComputer that they had shared their decryptor with law enforcement, so they could help victims recover their files.
“We shared our findings early with relevant law enforcement and intelligence partners and will continue to collaborate with the relevant organizations to affect the economics of the ransomware space in favor of defenders,” SentinelLabs told BleepingComputer.
Despite its weaknesses, the use of the Linux variant in actual Clop attacks demonstrates that, for the threat actors, having a Linux version, even one that’s easy to compromise, is still preferable to not being able to attack Linux systems within the target organizations.



