Catch up on the highlights of last week’s cybersecurity conference
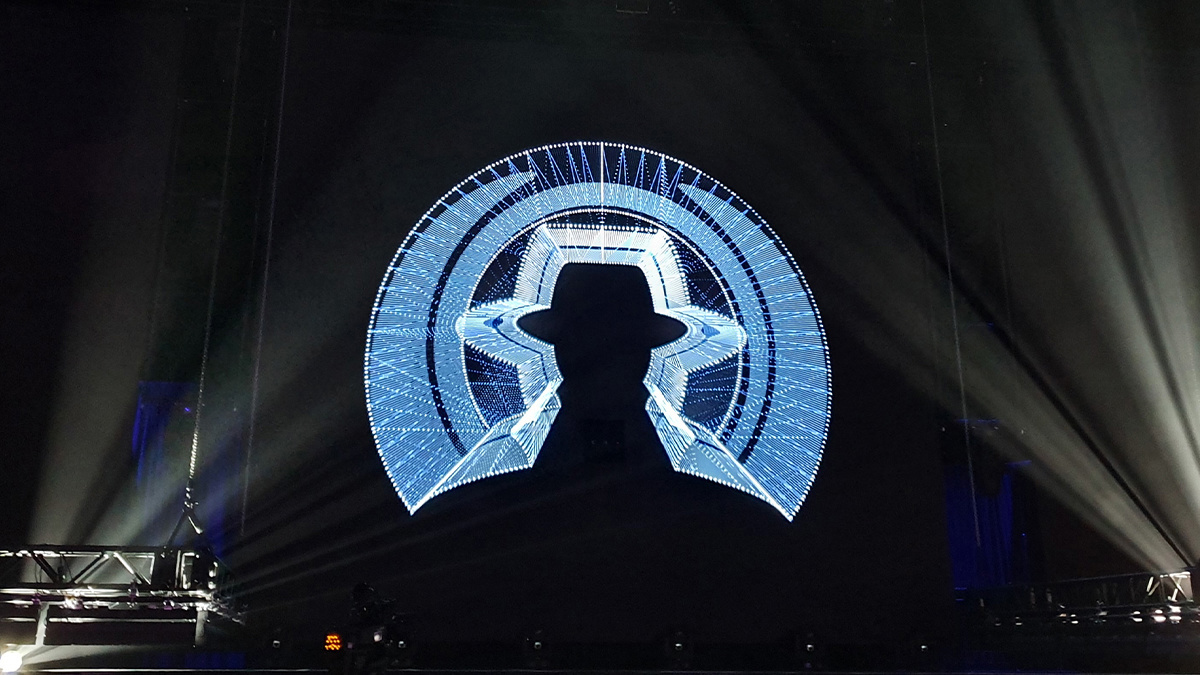
Alongside the release of hacking tools and a thought-provoking keynote, there was plenty on offer for web security professionals among the briefings at Black Hat Europe last week.
Vulnerability researchers often leave out the gnarly bits in talks that focus on their success in finding vulnerabilities, but a pair of hackers from Trellix gave a talk on how to learn from missteps and failures along the way.
Apparent failures can offer salutary lessons and – mixed with no little grit and persistence –eventually result in significant discoveries, researchers Douglas McKee and Philippe Laulheret told Black Hat delegates.
The session – ‘Fail Harder: Finding Critical 0-Days in Spite of Ourselves’ – took a “deep dive into all the things that didn’t work, along with the many challenges that preceded the findings of critical zero-day bugs across multiple projects”.
Among other things, the researchers explained how “failing harder” requires “lots of time spent researching systems before they can be hacked”.

Ethics in social engineering
In another talk, Ragnhild ‘Bridget’ Sageng of Orange Cyberdefence explored the ethics of using social engineering in penetration tests.
Such tests attempt to raise employee awareness about phishing attacks, but if not well thought through they can be counterproductive – especially if workers are left feeling duped or blamed for failures. Playing the blame game runs counter to fostering a productive learning experience, Sageng argued.
After all, the results of such tests have shown that even security professionals can fall victim to phishing lures, hence the need to increase focus on the (often neglected) post-engagement process.
Wif WAF
Back in the arena of finding vulnerabilities in technology, researcher Noam Moshe from Claroty’s Team82 explained how they discovered that a range of web application firewalls (WAFs) could be rendered blind to SQL injection payloads.
The issue – which stemmed from a failure to support JSON syntax in the SQL injection inspection process – affected technology from five leading vendors: Palo Alto Networks, Amazon Web Services, Cloudflare, F5, and Imperva. All five fixed the problem after Claroty highlighted the issue, as explained in more depth by The Daily Swig last week.
Delivering Parcels
Deserialization flaws have yielded a steady stream of issues for traditional apps over recent years. The hacking technique has also proven a problem for Android-based mobile systems.
During a presentation at Black Hat Europe, a team of engineers from Google outlined the evolution of Android Parcels, a technology designed to manage cross-process interaction and clamp down on bugs that arise from deserialization.
Bohemian hack story
Active defense has been discussed as an approach to thwart cyber-attacks orchestrated by nation states for several years. The details of how such an approach might work in practice have been shrouded in secrecy, but a talk by two threat intel experts from the state treasury of the Czech Republic showed how a combination of threat intelligence and active defense was used to thwart a series of attacks blamed on Russia.
The analysts explained that it was only by continuously improving their threat model and fine tuning their approach that they were able to make improvements in making critical information infrastructure more resilient.
Binded by the light
Web security researchers and bug hunters were offered insights into how it might be possible to hack web-based frameworks by abusing DataBinding.
DataBinding is used to bind request parameters to a domain object.
The approach is supported by a variety of programming frameworks, including Java, JavaScript, Groovy, Python, and Ruby.
However, implementation flaws in databinding have spawned a number of flaws in platforms including Spring, Struts, Grails, and Ruby on Rails.
Haowen Mu and Biao He from Ant Security FG Lab explained how the insecurity of the DataBinding mechanism itself spawned the infamous Spring4Shell, among other flaws, during their presentation at Black Hat.
YOU MAY ALSO LIKE Black Hat Europe 2022: Hacking tools showcased at annual security conference


