
A security researcher has found a way to exploit the data deletion capabilities of widely used endpoint detection and response (EDR) and antivirus (AV) software from Microsoft, SentinelOne, TrendMicro, Avast, and AVG to turn them into data wipers.
Wipers are a special type of destructive malware that purposely erases or corrupts data on compromised systems and attempts to make it so that victims cannot recover the data.
SafeBreach researcher Or Yair came up with the idea to exploit existing security tools on a targeted system to make the attacks more stealthy and remove the need for a threat actor to be a privileged user to conduct destructive attacks.
Also, abusing EDRs and AVs for data wiping is a good way to bypass security defenses as the file deletion capabilities of security solutions are expected behavior and would likely be missed.
Triggering the (wrong) deletion
Antivirus and EDR security software constantly scan a computer’s filesystem for malicious files, and when malware is detected, attempt to quarantine or delete them.
Furthermore, with real-time protection enabled, as a file is created, it is automatically scanned to determine if it is malicious and, if so, deleted/quarantined.
“There are two main events when an EDR deletes a malicious file. First, the EDR identifies a file as malicious and then it deletes the file,” explained Yair in his report.
“If I could do something between these two events, using a junction, I might be able to point the EDR towards a different path. These are called time-of-check to time-of-use (TOCTOU) vulnerabilities.
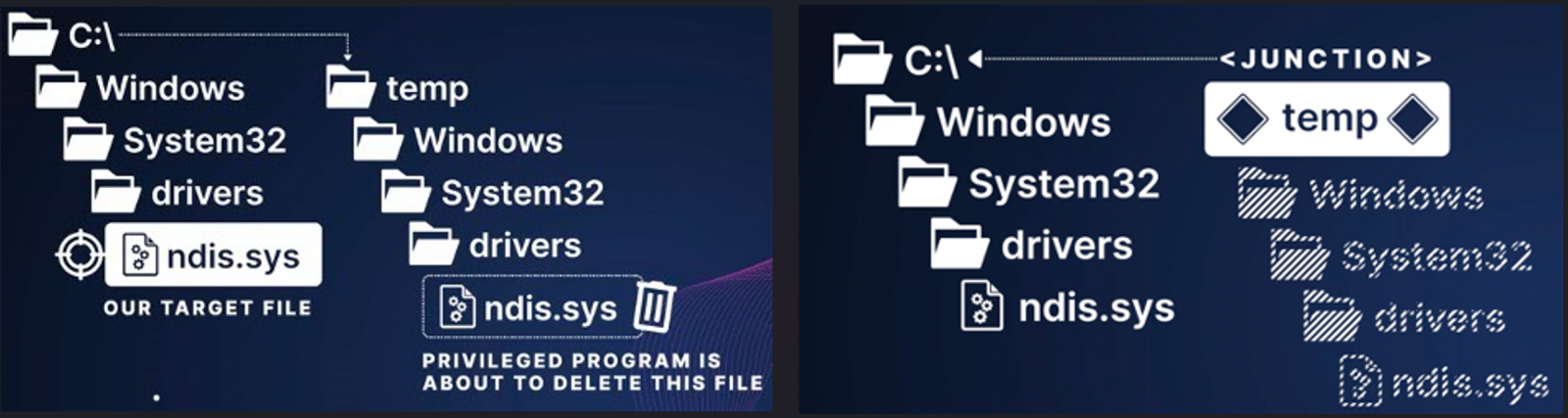
Yair’s idea was to create a C:tempWindowsSystem32drivers folder and store the Mimikatz program in the folder as ndis.sys.
As Mimikatz is detected by most EDR platforms, including Microsoft Defender, the plan was for it to be detected as malicious on creation. However, before the EDR could delete the file, the researcher would quickly delete the C:Temp folder and create a Windows Junction from C:Temp to C:Windows.
The hope was that the EDR would attempt to delete the ndis.sys file, which due to the junction, is now pointing to the legitimate C:Windowssystem32driversndis.sys file.
This didn’t work because some EDRs prevented further access to a file, including deletion, after it was detected as malicious. In other cases, EDRs detected the deletion of the malicious file, so the software dismissed the pending wiping action.
The solution was to create the malicious file, hold its handle by keeping it open, and not define what other processes are allowed to write/delete it so that EDRs and AVs detecting it can’t wipe it.
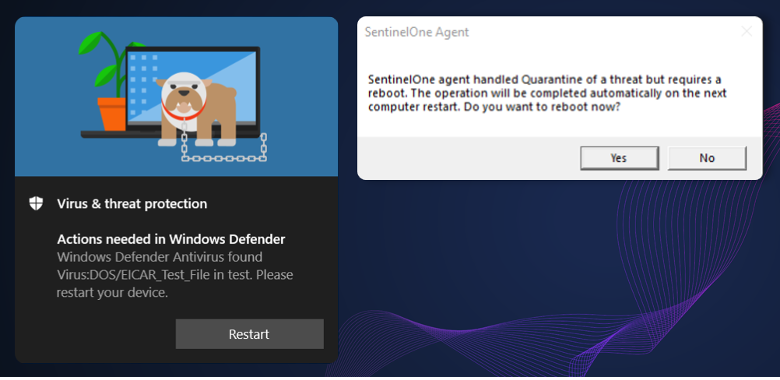
After the detection was triggered and having no rights to delete the file, the security tools prompted the researcher to approve a system reboot that would release the handle, freeing the malicious file for deletion.
The file deletion command, in this case, is written under the PendingFileRenameOperations Registry registry value, which will cause it to be deleted during the reboot.
However, when deleting the files in this value, Windows deletes the files while “blindly” following junctions.
“But what’s surprising about this default Windows feature is that once it reboots, Windows starts deleting all the paths and blindly follows junctions,” warned Yair.
Hence, by implementing the following five-step process, Yair could delete files in a directory he didn’t have modification privileges.
- Create a special path with the malicious file at C:tempWindowsSystem32driversndis.sys
- Hold its handle and force the EDR or AV to postpone the deletion until after the next reboot
- Delete the C:temp directory
- Create a junction C:temp → C:
- Reboot when prompted.
“This exploit is also effective for a ransomware protection feature in Windows called the Controlled Folder Access. This feature prevents untreated processes from modifying or deleting any files contained inside one of the folders listed in the Protected Folders list. However, since an EDR or AV is the most trusted entity on a system, this feature does not prevent them from deleting these files.” – SafeBreach.
The analyst implemented the exploit into a wiper tool he named “Aikido Wiper,” which is fully undetectable, can be launched by unprivileged users to wipe data on admin user directories, and can even make the system unbootable.
Impact and response
Yair tested the exploit against 11 security tools and found that Microsoft Defender, Defender for Endpoint, SentinelOne EDR, TrendMicro Apex One, Avast Antivirus, and AVG Antivirus were all vulnerable.
Security solutions that were not exploitable include Palo Alto, Cylance, CrowdStrike, McAfee, and BitDefender, which the analyst also tested.

Aikido features exploits for vulnerabilities found in Microsoft Defender, Defender for Endpoint, and SentinelOne EDR because they were the easiest to implement on the wiper tool.
Yair reported the flaws to all vulnerable vendors between July and August 2022, and they have all released fixes by now.
The vulnerability IDs assigned by the vendors for this issue are CVE-2022-37971 (Microsoft), CVE-2022-45797 (Trend Micro), and CVE-2022-4173 (Avast and AVG).
The fixed versions are:
- Microsoft Malware Protection Engine: 1.1.19700.2 or later
- TrendMicro Apex One: Hotfix 23573 & Patch_b11136 or later
- Avast & AVG Antivirus: 22.10 or later
All users of the above products are recommended to apply the security updates as soon as possible to mitigate the severe risk of having their files wiped by malware mimicking the Aikido wiper functionality.



