
A severe security flaw in the Amazon ECR (Elastic Container Registry) Public Gallery could have allowed attackers to delete any container image or inject malicious code into the images of other AWS accounts.
Amazon ECR Public Gallery is a public repository of container images used for sharing ready-to-use applications and popular Linux distributions, such as Nginx, EKS Distro, Amazon Linux, CloudWatch agent, and Datadog agent.
A Lightspin security analyst discovered a new flaw in the ECR Public Gallery where it’s possible to modify existing public images, layers, tags, registries, and repositories of other users by abusing undocumented API actions.
The researcher reported the vulnerability to AWS Security on November 15, 2022, and Amazon rolled out a fix in under 24 hours.
While there are no signs of this flaw being abused in the wild, threat actors could have used it in massive-scale supply chain attacks against many users.
Characteristically, the top six most downloaded container images in ECR Public Gallery have had over 13 billion downloads, so any malicious injection in them could have resulted in “out-of-control” infections.
Lightspin says its analysis showed that 26% of all Kubernetes clusters have at least one pod that pulls an image from ECR Public Gallery, so the repercussions could have been significant.
Leveraging undocumented API actions
Lightspin’s researcher discovered that ECR Public Gallery had several internal API actions used for supporting specific commands and user actions but which aren’t exposed publicly.
Four of these API actions, listed below, did not have any triggers, yet they were still active on the platform and hence could be invoked.
- DeleteImageForConvergentReplicationInternal
- DeleteTagForConvergentReplicationInternal
- PutImageForConvergentReplicationInternal
- PutLayerForConvergentReplicationInternal
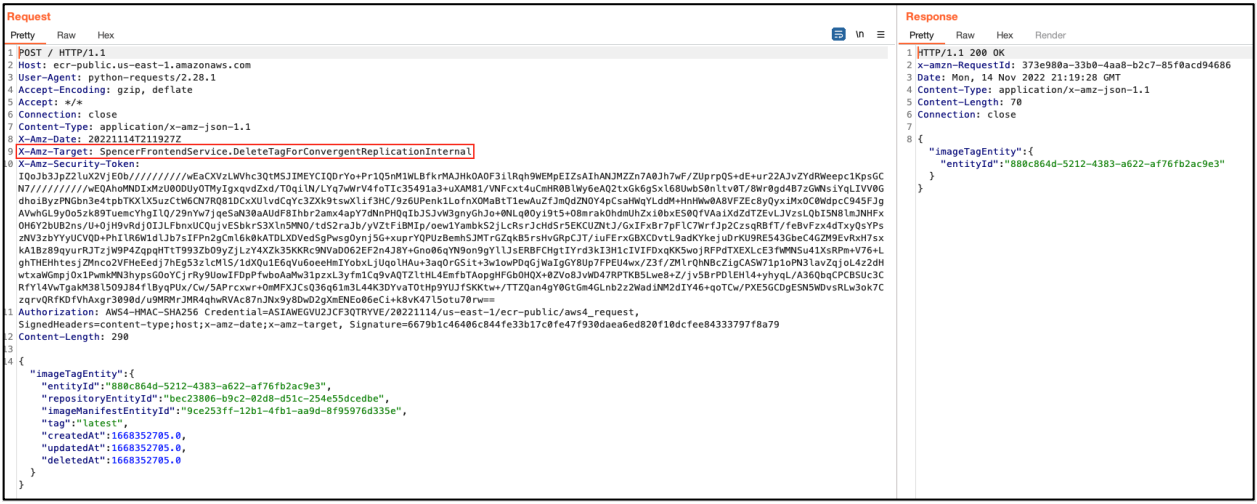
After figuring out a way to authenticate against the ECR internal API using temporary credentials from Amazon Cognito, the analyst forged malicious API requests that would be accepted.
Of course, for the above to work, the request should have a valid JSON structure, and since there was no documentation for these API calls, deducing it required some experimentation.
In the proof of concept example provided in Lightspin’s report, the request uses the “DeleteImage” API call and publicly available repository and image IDs to wipe a publicly available image uploaded by the researcher.
The researcher baked the exploit steps into a Python script, so the process could have been automated to abuse the undocumented API calls to attack public images.
Amazon’s Response
Amazon told BleepingComputer that they immediately remediated the issue discovered by Lightspin, and the internal investigation has revealed no signs of exploitation by malicious actors.
Based on the examined logs and evidence, the internet giant is confident that no customer accounts, uploads, or other assets have been compromised.
Amazon’s complete statement is below:
On November 14, 2022, a security researcher reported an issue in Amazon Elastic Container Registry (ECR) Public Gallery, a public website for finding and sharing public container images. The researcher identified an ECR API action that, if called, could have enabled modification or removal of images available on ECR Public Gallery.
As of November 15, 2022, the identified issue was remediated. We have conducted exhaustive analysis of all logs. We are confident our review was conclusive, and that the only activity associated with this issue was between accounts owned by the researcher. No other customers’ accounts were affected, and no customer action is required. We would like to thank Lightspin for reporting this issue.



