
Over 5.4 million Twitter user records containing non-public information stolen using an API vulnerability fixed in January have been shared for free on a hacker forum.
Another massive, potentially more significant, data dump of millions of Twitter records has also been disclosed by a security researcher, demonstrating how widely abused this bug was by threat actors.
The data consists of scraped public information as well as private phone numbers and email addresses that are not meant to be public.
The Twitter data breach
Last July, a threat actor began selling the private information of over 5.4 million Twitter users on a hacking forum for $30,000.
While most of the data consisted of public information, such as Twitter IDs, names, login names, locations, and verified status, it also included private information, such as phone numbers and email addresses.
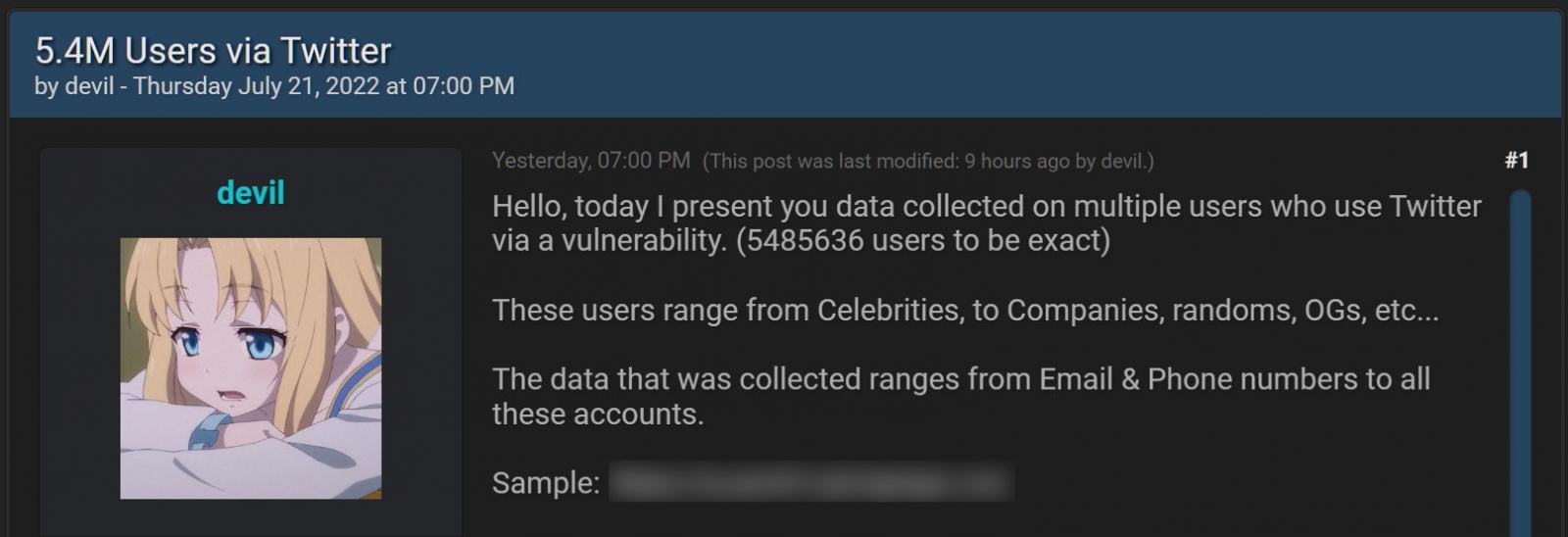
Source: BleepingComputer
This data was collected in December 2021 using a Twitter API vulnerability disclosed in the HackerOne bug bounty program that allowed people to submit phone numbers and email addresses into the API to retrieve the associated Twitter ID.
Using this ID, the threat actors could then scrape public information about the account to create a user record containing both private and public information, as shown below.
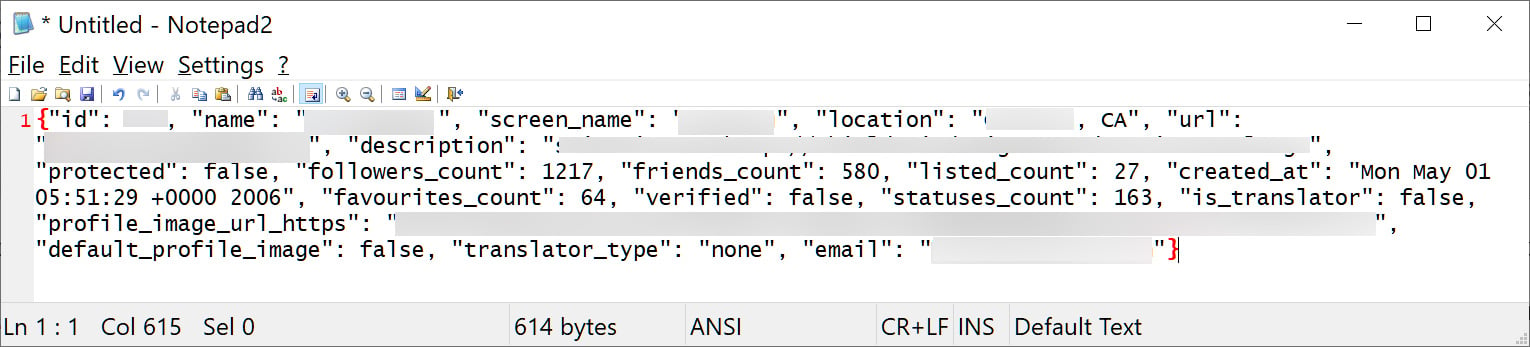
Source: BleepingComputer
It is unclear if the HackerOne disclosure was leaked, but BleepingComputer was told that multiple threat actors were utilizing the bug to steal private information from Twitter.
After BleepingComputer shared a sample of the user records with Twitter, the social media company confirmed they had suffered a data breach using an API bug fixed in January 2022.
Pompompurin, the owner of the Breached hacking forum, told BleepingComputer this weekend that they were responsible for exploiting the bug and creating the massive dump of Twitter user records after another threat actor known as ‘Devil’ shared the vulnerability with them.
In addition to the 5.4 million records for sale, there were also an additional 1.4 million Twitter profiles for suspended users collected using a different API, bringing the total to almost 7 million Twitter profiles containing private information.
Pompompurin said that this second data dump was not sold and was only shared privately among a few people.
Twitter data shared on a hacking forum
In September, and now more recently, on November 24th, the 5.4 million Twitter records have now been shared for free on a hacking forum.
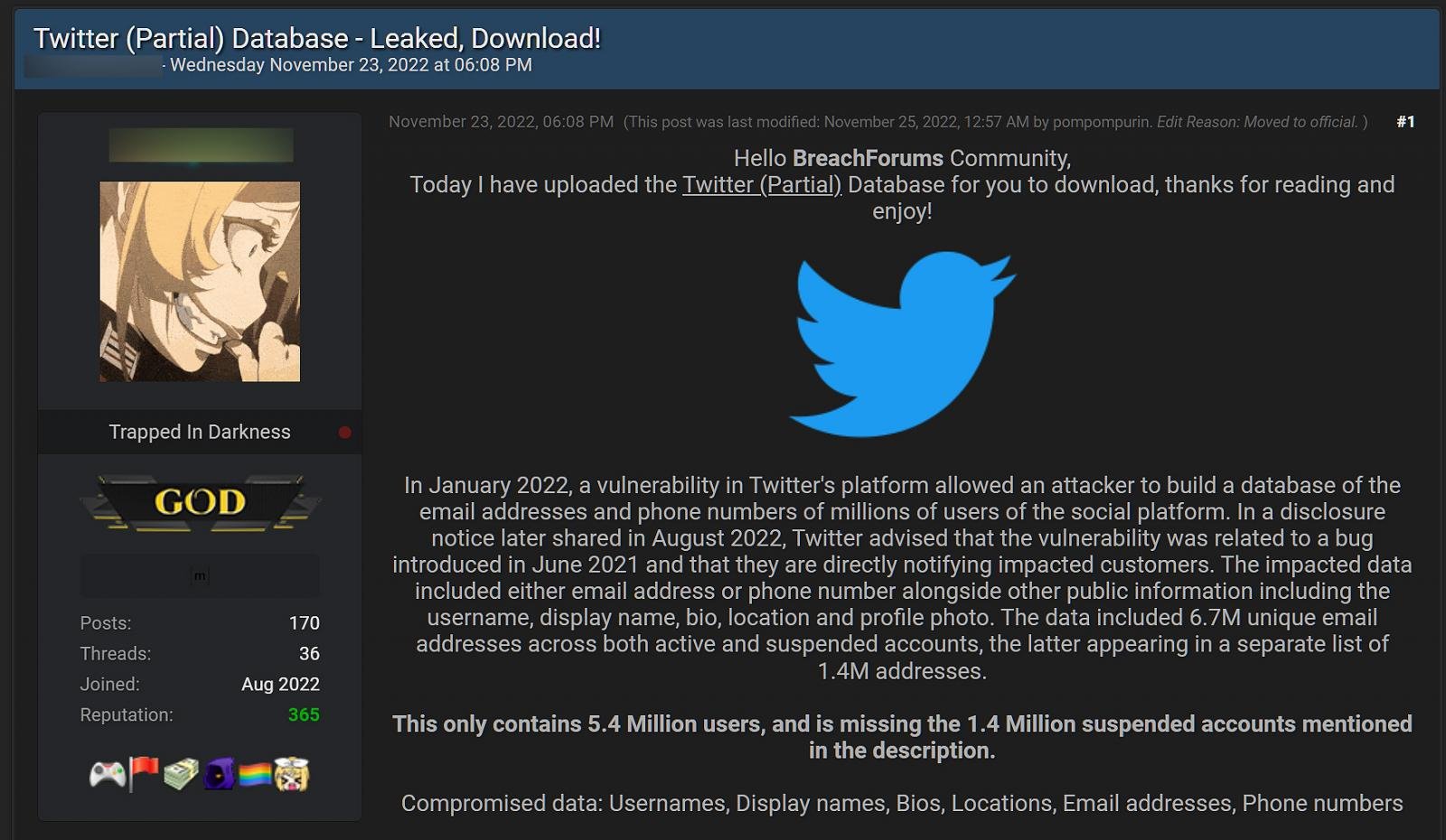
Source: BleepingComputer
Pompompurin has confirmed to BleepingComputer that this is the same data that was for sale in August, and includes 5,485,635 Twitter user records.
These records contain either a private email address or phone number, and public scraped data, including the account’s Twitter ID, name, screen name, verified status, location, URL, description, follower count, account creation date, friends count, favorites count, statuses count, and profile image URLs.
An even larger data dump privately created
While it is concerning that threat actors released the 5.4 million records for free, an even larger data dump was allegedly created using the same vulnerability.
This data dump potentially contains tens of millions of Twitter records consisting of personal phone numbers collected using the same API bug, and public information, including verified status, account names, Twitter ID, bio, and screen name.
The news of this more significant data breach comes from security expert Chad Loder, who first broke the news on Twitter and was suspended soon after posting. Loder subsequently posted a redacted sample of this larger data breach on Mastodon.
“I have just received evidence of a massive Twitter data breach affecting millions of Twitter accounts in EU and US. I have contacted a sample of the affected accounts and they confirmed that the breached data is accurate. This breach occurred no earlier than 2021,” Loder shared on Twitter.
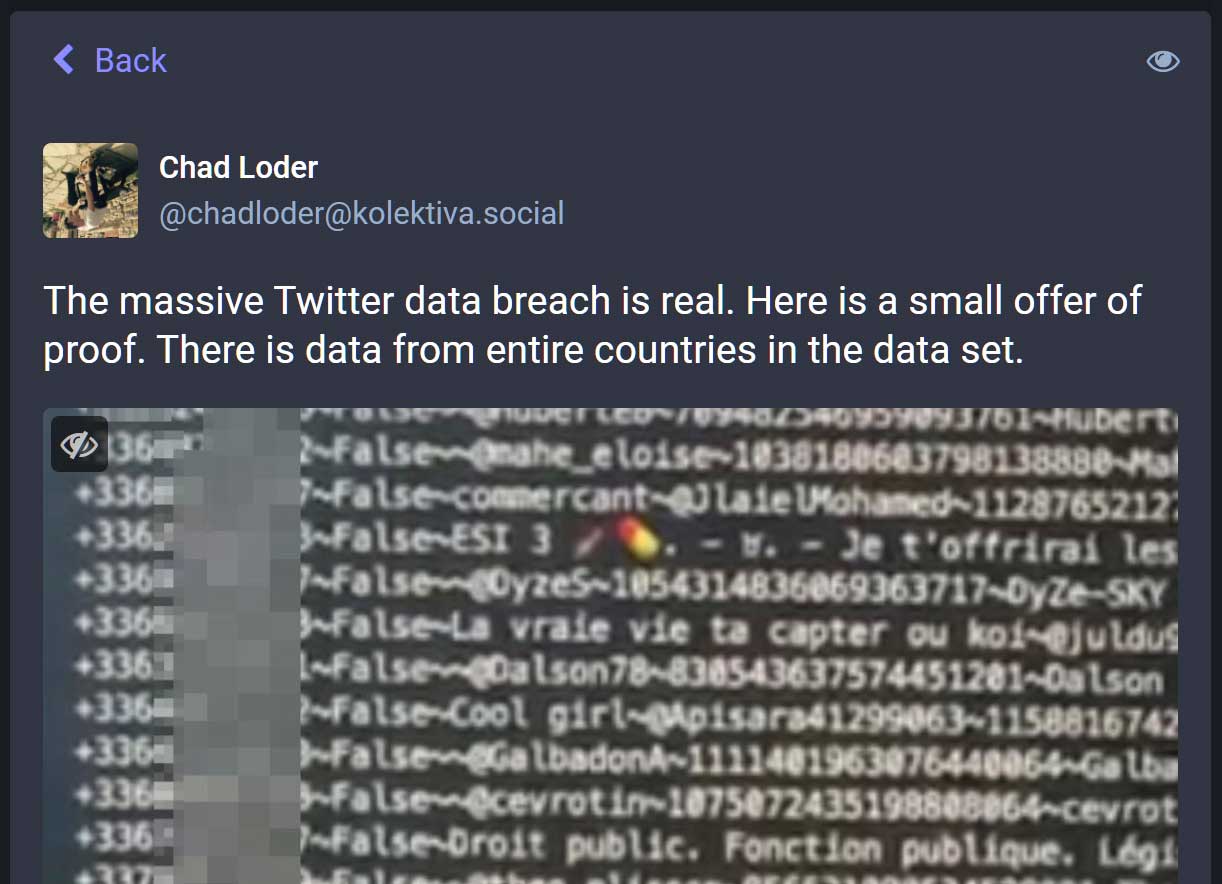
Source: BleepingComputer
BleepingComputer has obtained a sample file of this previously unknown Twitter data dump, which contains 1,377,132 phone numbers for users in France.
We have since confirmed with numerous users in this leak that the phone numbers are valid, verifying this additional data breach is real.
Furthermore, none of these phone numbers are present in the original data sold in August, illustrating how much larger Twitter’s data breach was than previously disclosed and the large amount of user data circulating among threat actors.
Pompompurin also confirmed with BleepingComputer that they were not responsible and did not know who created this newly discovered data dump, indicating that other people were using this API vulnerability.
BleepingComputer has learned that this newly discovered data dump consists of numerous files broken up by country and area codes, including Europe, Israel, and the USA.
We were told that it consists of over 17 million records but could not independently confirm this.
As this data can be potentially used for targeted phishing attacks to gain access to login credentials, it is essential to scrutinize any email that claims to come from Twitter.
If you receive an email claiming your account was suspended, there are log in issues, or you are about to lose your verified status, and it prompts you to login on to a non-Twitter domain, ignore the emails and delete them as they are likely phishing attempts.
BleepingComputer reached out to Twitter on Thursday about this additional data dump of private information but has yet to receive a response.



