Mobile Hacker For Hire
Are you in need of a hacker?
Mobile Hacker For Hire provides hacking services to any and everyone. Our range of services is basically unlimited. We are continuously adding new features to our platform to keep up with the needs of our clients. So, if you’re looking for a professional hacker, MobileHackerForHire is your go-to choice.
Mobile Hacker For Hire
Hire A Hacker Service
MobileHackerForHire is a group of highly trained hackers offering hacking services to individuals and businesses worldwide. The crew maintains an elite status in the hacker community, ensuring that all their work is done in the most professional and discreet manner possible. If you have any issues regarding online privacy, online identity or security, hiring this team for internet security consultancy would be your best choice.

Service

Service
Service
Catch a cheating spouse
Phone hacker for hire
A perfect tool for getting evidence on someone cheating on their partner or spouse.
When you hire MobileHackerForHire, you will receive a hack of your choice within a specified time frame. They use advanced hacking tools and techniques to hack the devices of your target, and they guarantee fast results. Without any doubts, MobileHackersForHire is the best team of professional hackers all over the world.
Immediate Results
No Hacking Skills Required
No matter where they are
Why Choose Us
Easily Investigate Cell Phone Activity
Curious about what is happening behind closed doors? Hire a hacker. You can now monitor calls on both sides of the line and check text messages from any phone number!
Professional Hackers for hire
Frequently Asked Questions
Can I hire a hacker to spy on my spouse's phone?
If you are not sure if your spouse is cheating on you, then there is no option but to hire a hacker. Almost every woman is quite curious to be with the same person in case the guy they are currently married to starts cheating on them. If you are looking for a trustworthy and accurate hacker, look no further than MobileHackerForHire.
Where do I hire professional hackers?
If you are in the hunt for a professional hacker, you need to look nowhere else. MobileHackerForHire is the best mobile hacking service provider in this digital era. With reasonable prices and guaranteed results, you will not find better for hacking devices! So, if you want to hack a device, do not waste your time
Is there any way to hire a hacker to get my account back?
Yes! We can help you get any account back—as long as you have access to that person's email address or phone number (and they haven't changed it yet). Just contact us with what you need and we'll take care of it immediately!
Where do I hire a hacker aside from the dark web?
MobileHackerForHire is a reputed cyber security organization that has helped people in various circumstances. This company has gained the trust of thousands upon thousands of customers, as well as industry experts, by providing consistent and efficient services. Through their expertise, they have provided reliable solutions to clients around the globe.
Can WhatsApp be hacked?
Yes, it can. Our team of hackers can hack into any kind of messaging app, including WhatsApp, Viber, LINE and more.
Can they really hack Facebook accounts?
Yes! This is one of our specialties, and it's not hard at all. All you need is the email address associated with the account and a little patience as we do our magic!
Hey there! You’re probably wondering why you should hire a hacker to recover your email, your Facebook, or your cryptocurrency. That’s a good question! Let’s take a look at some of the most common questions we get about hiring a hacker.
Hiring a hacker could be the difference between getting your ex-significant other back and not getting them back. It could be the difference between having an accident that ruins your life or getting away with it cleanly and in one piece.
It could even be the difference between getting into the good graces of your boss or losing your job altogether. Hiring a hacker can help you get what you want from life, but only if you know how to find one!
Catch A Cheating Partner
Hire a hacker on our platform today. Our experienced professional hackers will monitor all calls, texts, emails, and internet activity of your target phone remotely, without them ever knowing. You can trust us!
Free Consultation
Useful Resources
You can find all of the information you need about our services and recent exploits on this page, or if you have any questions about what we offer, please don’t hesitate to reach out.

- Date: October 7, 2023
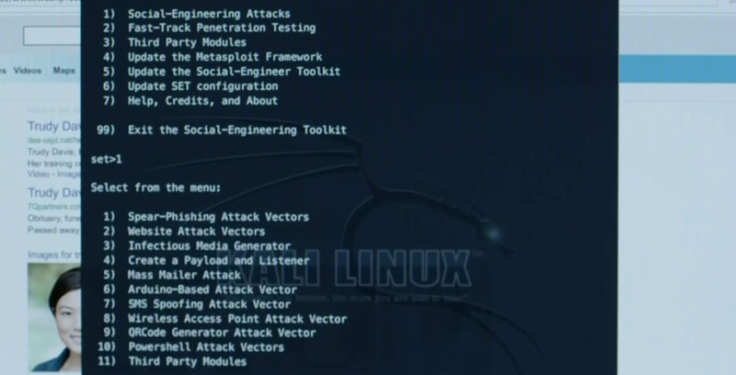
Mellon – OSDP Attack Tool
- 5 min read
- 0 comment
- Date: October 7, 2023
Dissect: Quickly Access And Analyse Forensic Artefacts From Various Disk And File Formats
- 4 min read
- 0 comment
Hire a hacker for cell phone!
Hire a hacker on our platform today. Our experienced professionals will monitor all calls, texts, emails, and internet activity of your target phone remotely, without them ever knowing. You can trust us!
